Splunk app for Wazuh
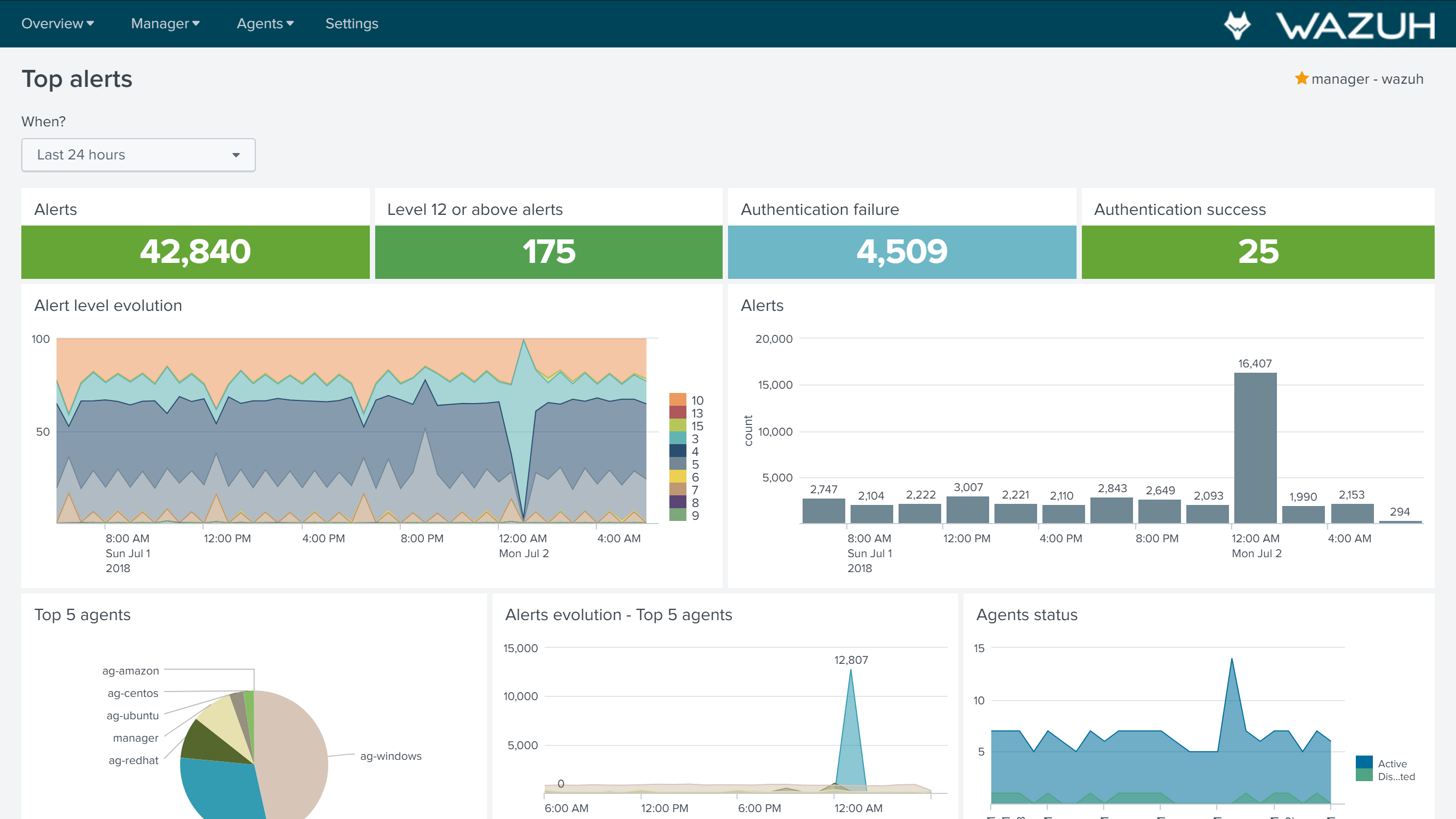
Wazuh app for Splunk offers an UI to visualize Wazuh alerts and API data. Wazuh helps you to gain deeper security visibility into your infrastructure by monitoring hosts at an operating system and application level.
Installation
Download the latest Splunk app for Wazuh:
curl -o SplunkAppForWazuh.tar.gz https://packages.wazuh.com/3.x/splunkapp/v3.4.0_7.1.2.tar.gz
Install the Splunk app for Wazuh:
The app uses the
/SplunkAppForWazuh/default/indexes.conffile to create an index named 'wazuh' and/SplunkAppForWazuh/default/inputs.conffile to listen to forwarded data on port 9997.Warning
In case you have an Indexer cluster, first delete indexes.conf and inputs.conf files to avoid index creation in the current instance, then install the app on the Search Head and configure a 'wazuh' index following the Splunk official documentation .
CLI mode:
# /opt/splunk/bin/splunk install app SplunkAppForWazuh.tar.gz# /opt/splunk/bin/splunk restart
Web GUI:
Apps -> Manage apps -> Install app from file
Open Splunk in your desired browser and click on the Wazuh app icon:
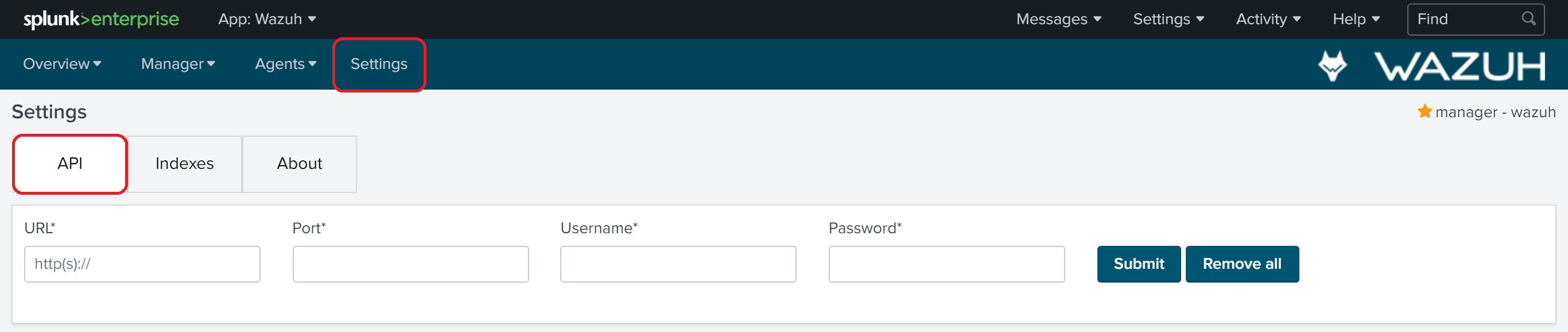
Fill in the Username and Password fields with your credentials; you can get more information about how to do this at Securing the Wazuh API. Enter
http(s)://MANAGER_IPfor the URL whereMANAGER_IPis the Wazuh manager IP address and use "55000" for the Port:
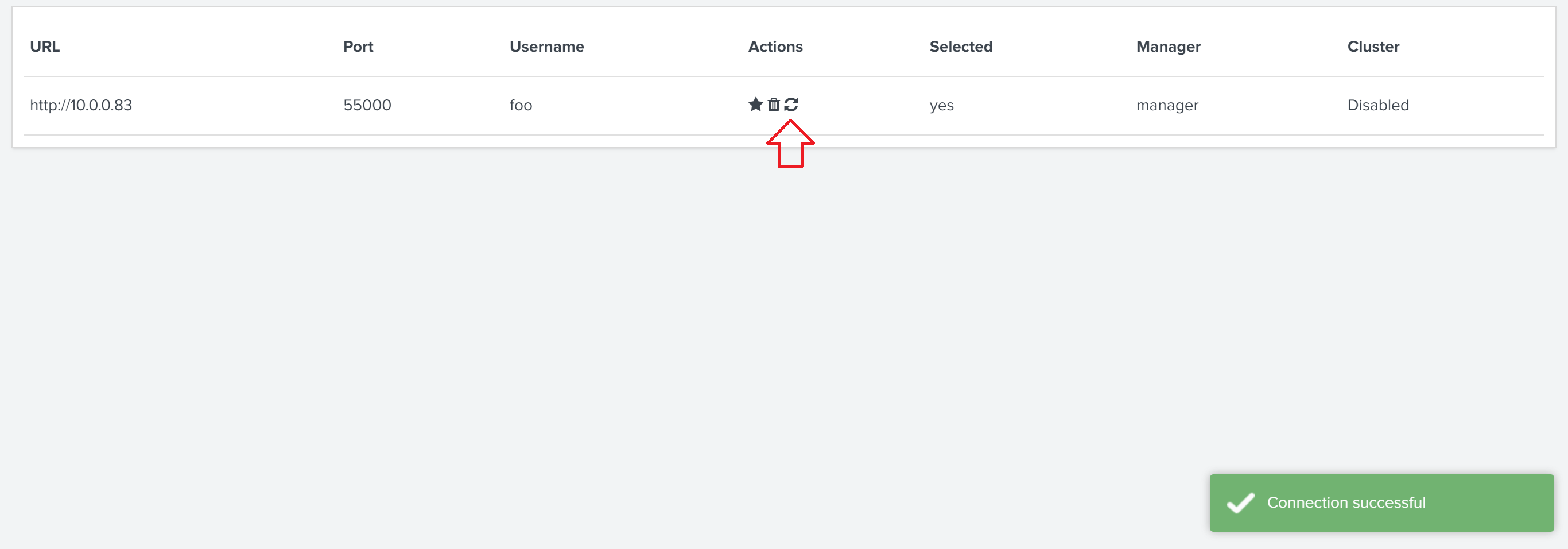
You can check the connection by pressing 'Check connection' button on each API entry. A successful message appears in the right bottom corner:
Now that you've finished installing Splunk app for Wazuh, you can setup forwarders following the next page.