Disabling a Linux user account with active response
Without knowledge of the password for an account, an adversary might opt to systematically guess the password using a repetitive or iterative mechanism. In this use case, we configure the disable-account active response to disable a Linux/Unix account subject to brute-force attacks. Wazuh uses the disable-account active response on Linux/Unix endpoints to disable the account for the user in the dstuser field of a Wazuh alert.
Infrastructure
Endpoint |
Description |
|---|---|
Ubuntu 22.04 |
The endpoint to monitor for brute-force attacks. |
Wazuh server
Add the rule below to the Wazuh server
/var/ossec/etc/rules/local_rules.xmlfile:<group name="pam,syslog,"> <rule id="100100" level="10" frequency="3" timeframe="120"> <if_matched_sid>5503</if_matched_sid> <description>Possible password guess on $(dstuser): 3 failed logins in a short period of time</description> <mitre> <id>T1110</id> </mitre> </rule> </group>
This rule checks for 3 failed authentication logins on the same user account within 2 minutes.
Open the Wazuh server
/var/ossec/etc/ossec.conffile and verify that a<command>block calleddisable-accountwith the following configuration is present within the<ossec_config>block:<command> <name>disable-account</name> <executable>disable-account</executable> <timeout_allowed>yes</timeout_allowed> </command>
The
<command>block contains information about the action to be executed on the Wazuh agent.<name>: Sets a name for the command. In this case,disable-account.<executable>: Specifies the active response script that must run after a trigger. In this case, it’s thedisable-accountexecutable.<timeout_allowed>: Allows a timeout after a period of time. This tag is set toyeshere, which represents a stateful active response.
Add the
<active-response>block below to the Wazuh server/var/ossec/etc/ossec.confconfiguration file:<ossec_config> <active-response> <command>disable-account</command> <location>local</location> <rules_id>100100</rules_id> <timeout>300</timeout> </active-response> </ossec_config>
<command>: Specifies the command to configure. This is the command namedisable-accountdefined in the previous step.<location>: Specifies where the command executes. Using thelocalvalue here means that the command executes on the monitored endpoint where the trigger event occurs.<rules_id>: The active response module executes the command if rule ID100100:Possible password guess on $(dstuser): 3 failed logins in a short period of timefires.<timeout>: Specifies how long the active response action must last. In this use case, we configure it to last for 300 seconds. After that period, the active response reverts its action and re-enables the account.
Restart the Wazuh manager service to apply changes:
$ sudo systemctl restart wazuh-manager
Ubuntu endpoint
Create two users for testing purposes:
$ sudo adduser user1 $ sudo adduser user2
Test the configuration
To test our use case, sign in to the user1 account and attempt to switch to user2 using a wrong password. Then verify that the user2 account is disabled, and the related alerts are displayed on the Wazuh dashboard.
Switch to
user1using the correct password:$ su user1
As
user1, run the following commands three(3) times and type in any wrong password foruser2when prompted to enter the password:$ su user2
Check that the account was successfully locked using the
passwdcommand:$ sudo passwd --status user2
user2 L 02/20/2023 0 99999 7 -1
The
Lflag indicates the account is locked.
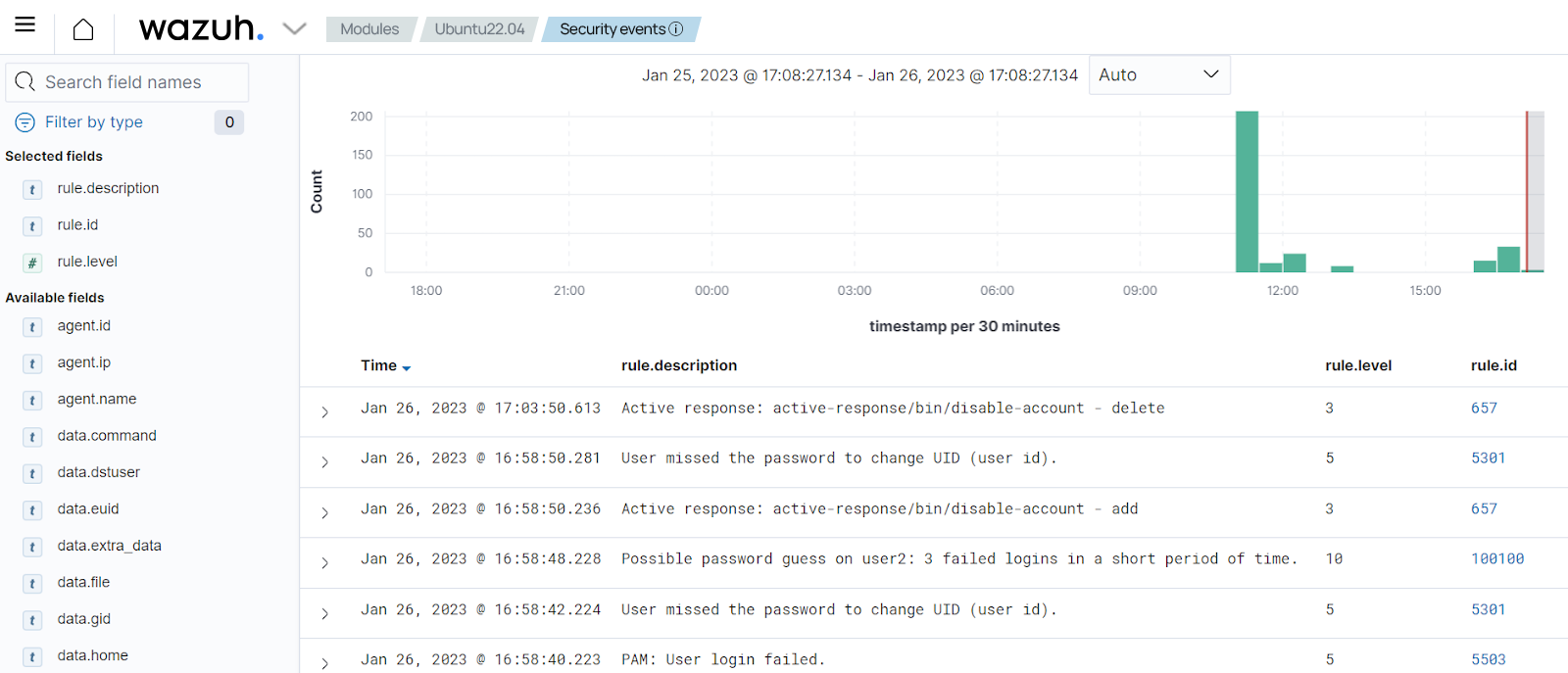
Visualize the alerts
You can visualize the alert data on the Wazuh dashboard. In the image below, you can see that the active response triggers just after rule ID 100100 fires to disable the account. Then re-enables it again after 5 minutes.