Amazon VPC
Amazon Virtual Private Cloud (Amazon VPC) lets you provision a logically isolated section of the AWS Cloud where you can launch AWS resources in a virtual network that you define. You have complete control over your virtual networking environment, including selection of your own IP address range, creation of subnets, and configuration of route tables and network gateways. You can use both IPv4 and IPv6 in your VPC for secure and easy access to resources and applications.
Amazon configuration
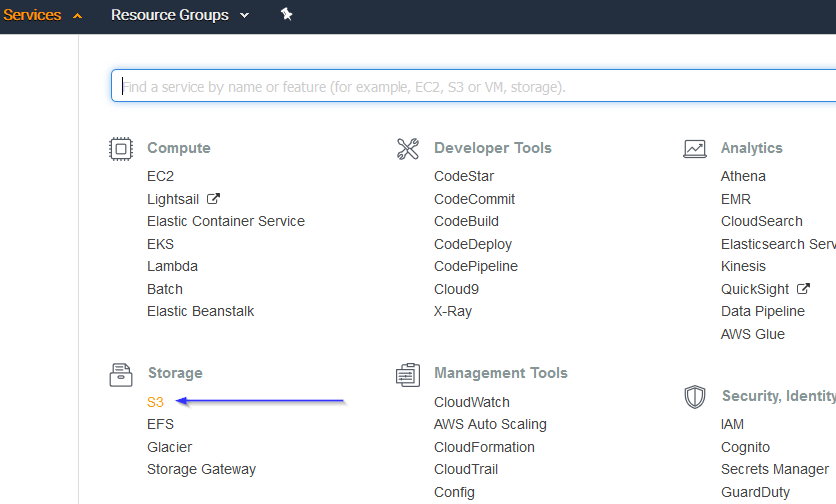
Go to Services > Storage > S3:
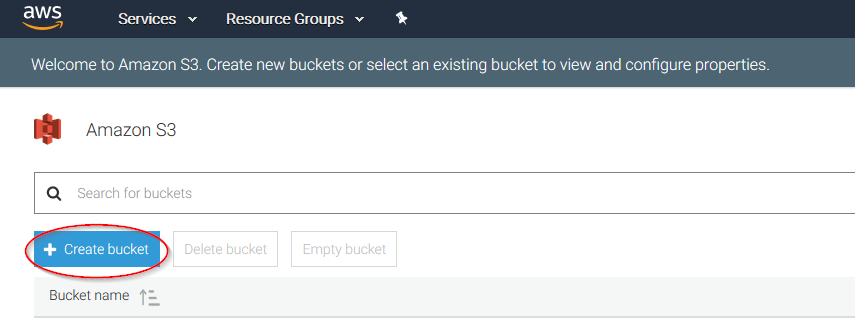
Click on the Create bucket:
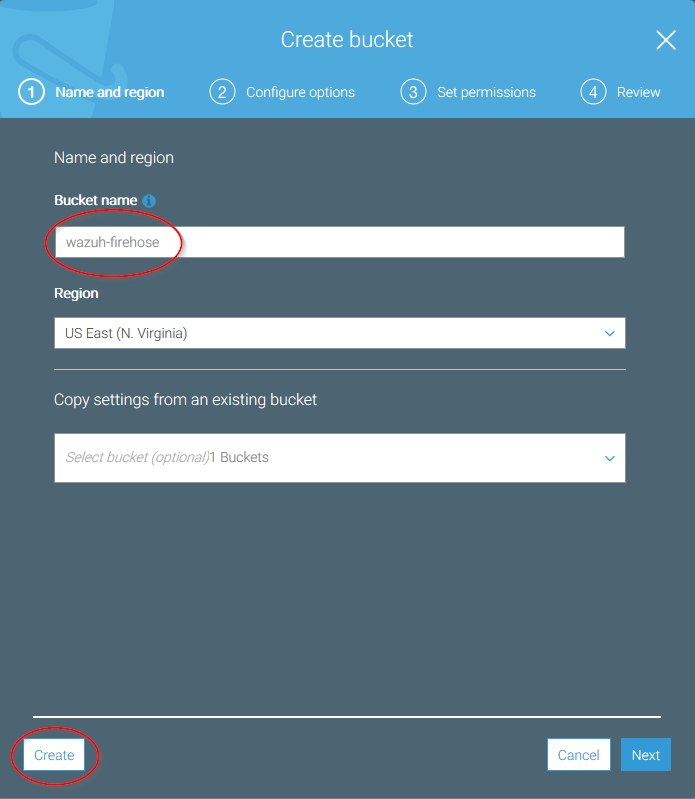
Create a new bucket, giving it a name and clicking on the Create button. Don't forget to save its Bucket ARN, you'll need it later in the process:
Go to Services > Compute > EC2:

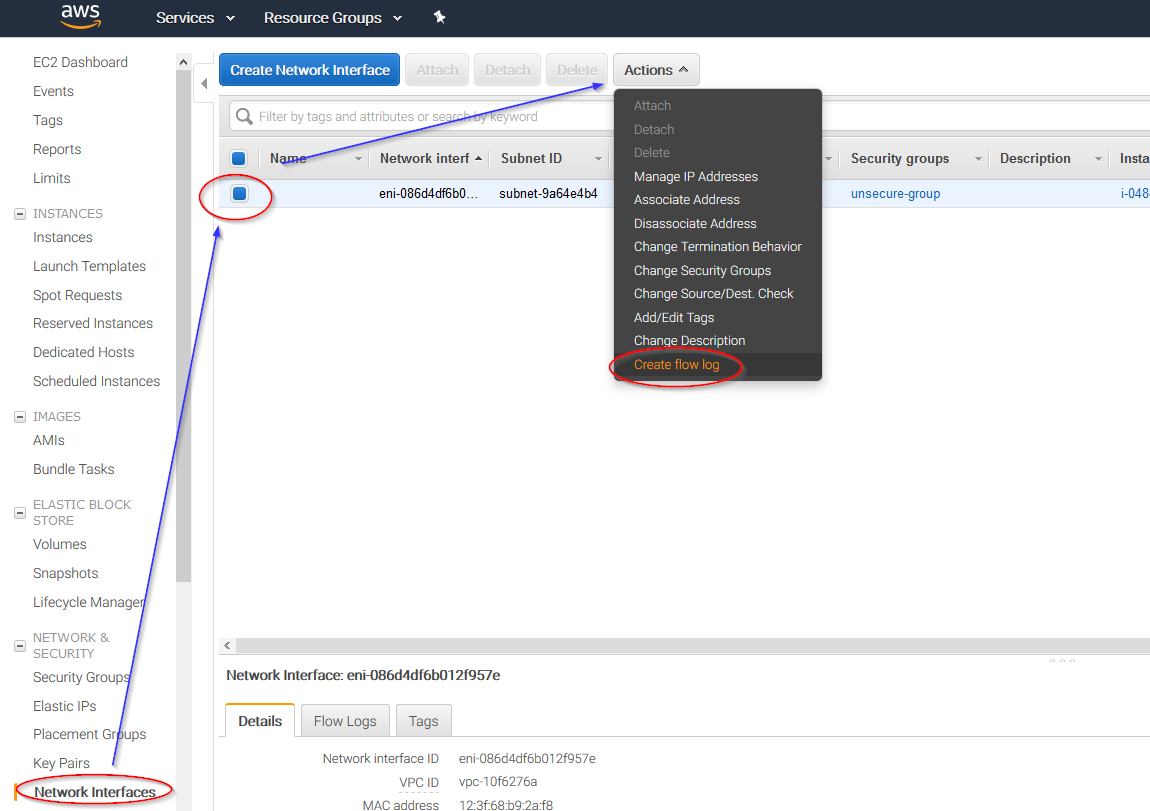
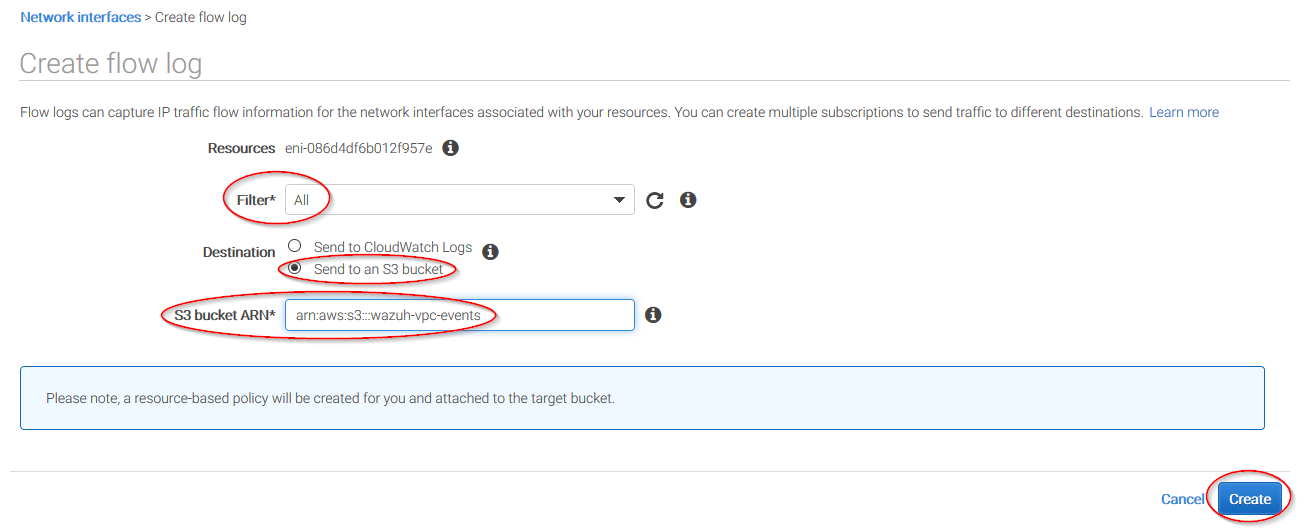
Go to Network & Security > Network Interfaces on the left menu. Select a network interface and select Create a flow log on the Actions menu:
Change all fields to look like the following screenshot and paste the ARN of the previously created bucket:
Wazuh configuration
Open the Wazuh configuration file (
/var/ossec/etc/ossec.conf) and add the following block:
<wodle name="aws-s3">
<disabled>no</disabled>
<interval>10m</interval>
<run_on_start>yes</run_on_start>
<skip_on_error>yes</skip_on_error>
<bucket type="vpcflow">
<name>wazuh-aws-wodle</name>
<path>vpc</path>
<aws_profile>default</aws_profile>
</bucket>
</wodle>
Note
Check the AWS S3 module reference manual to learn more about each setting.
Restart Wazuh in order to apply the changes:
If you're configuring a Wazuh manager:
For Systemd:
# systemctl restart wazuh-manager
For SysV Init:
# service wazuh-manager restart
If you're configuring a Wazuh agent:
For Systemd:
# systemctl restart wazuh-agent
For SysV Init:
# service wazuh-agent restart
Use cases
Using an Amazon VPC (Virtual Private Cloud), you can logically isolate some of your AWS assets from the rest of your cloud infrastructure. You can actually set up your own networks in the cloud. This is why, it is usually important to monitor changes to your VPCs.
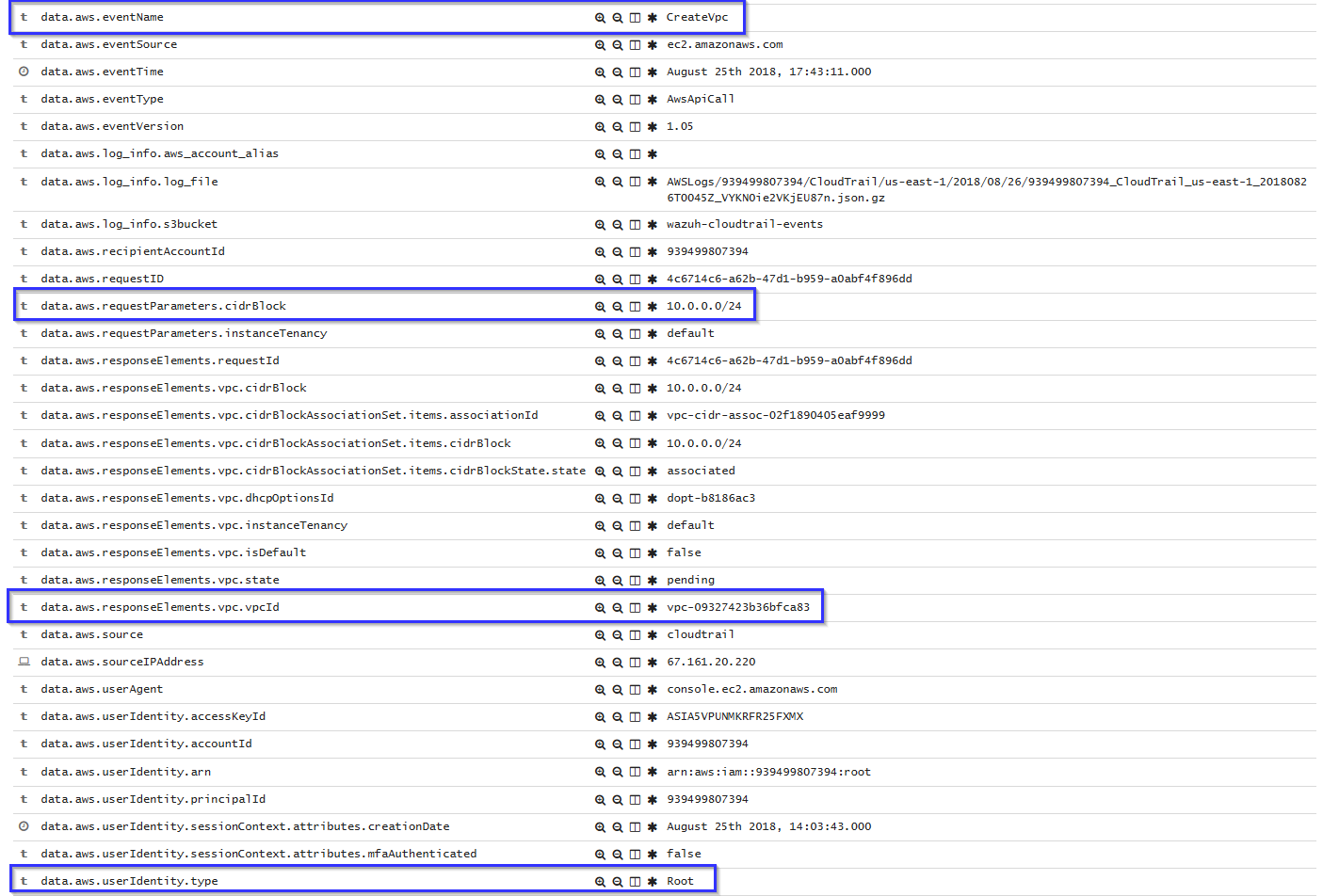
Create a VPC
If a VPC is created, the following alert will be shown on Kibana:
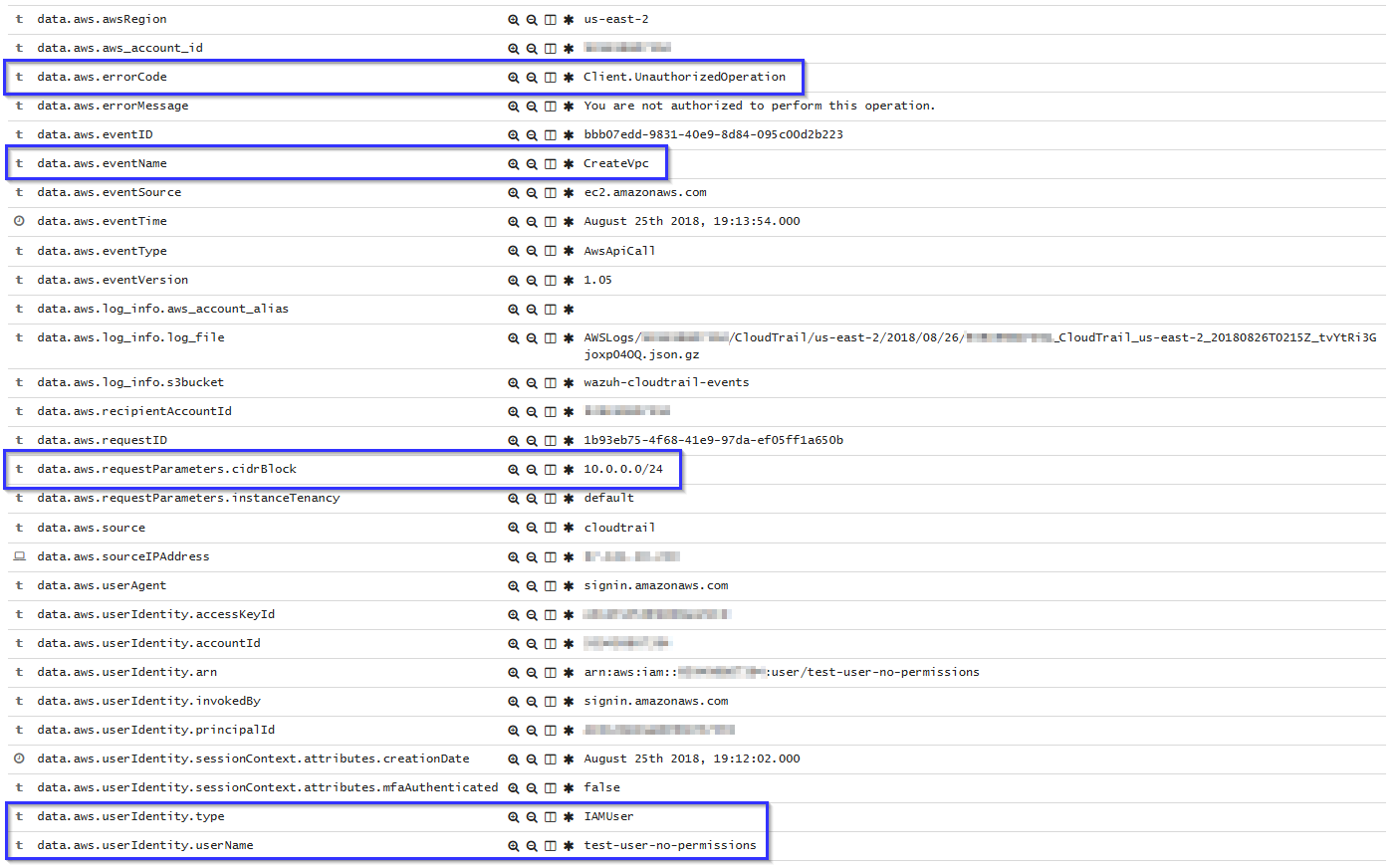
If a user without proper permissions attempts to create a VPC, the following alert will be shown on Kibana:
Working with VPC Data
A VPC alert contains data such as dest and source IP address, dst and source port and how many bytes were sent:
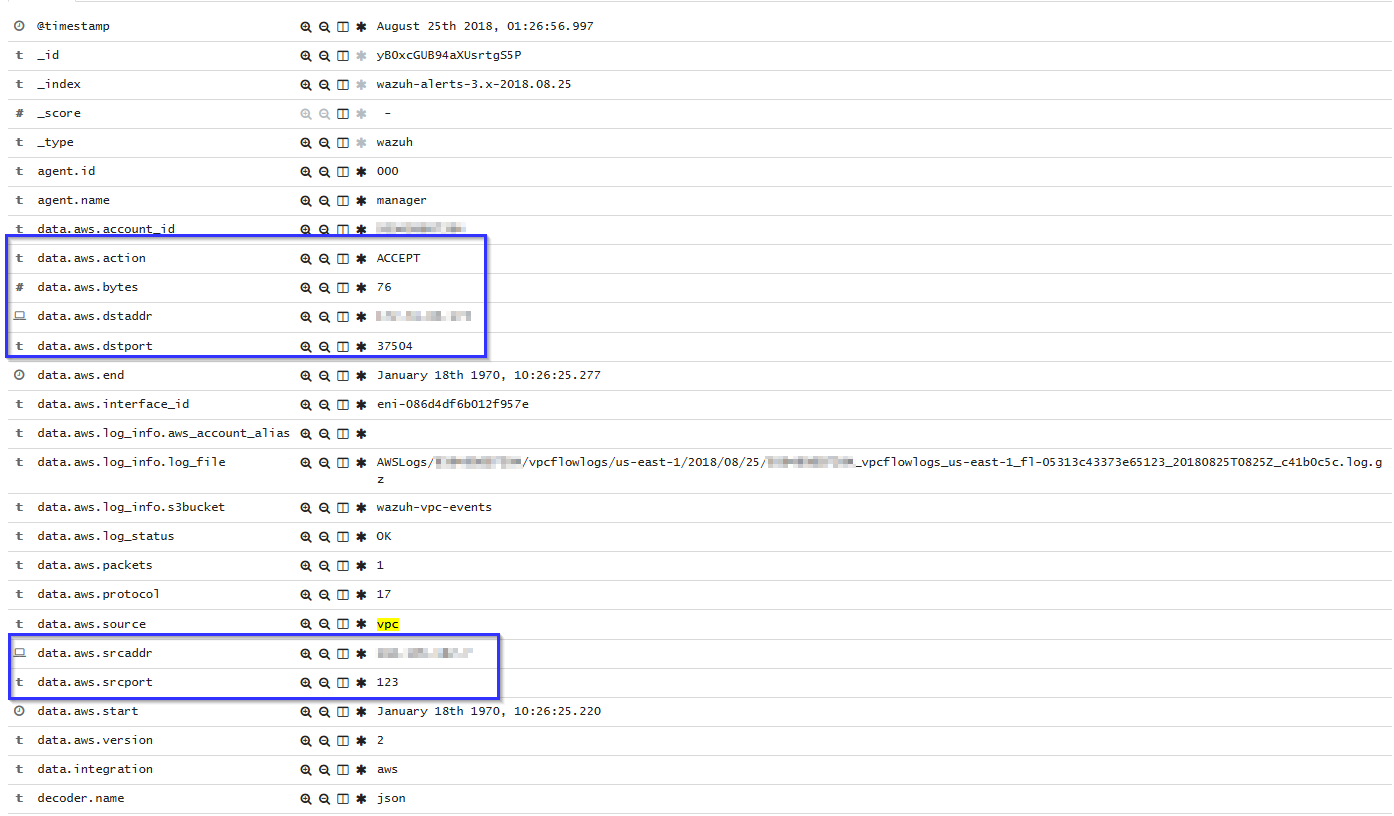
These alerts can be easily analyzed using visualizations like the following one:
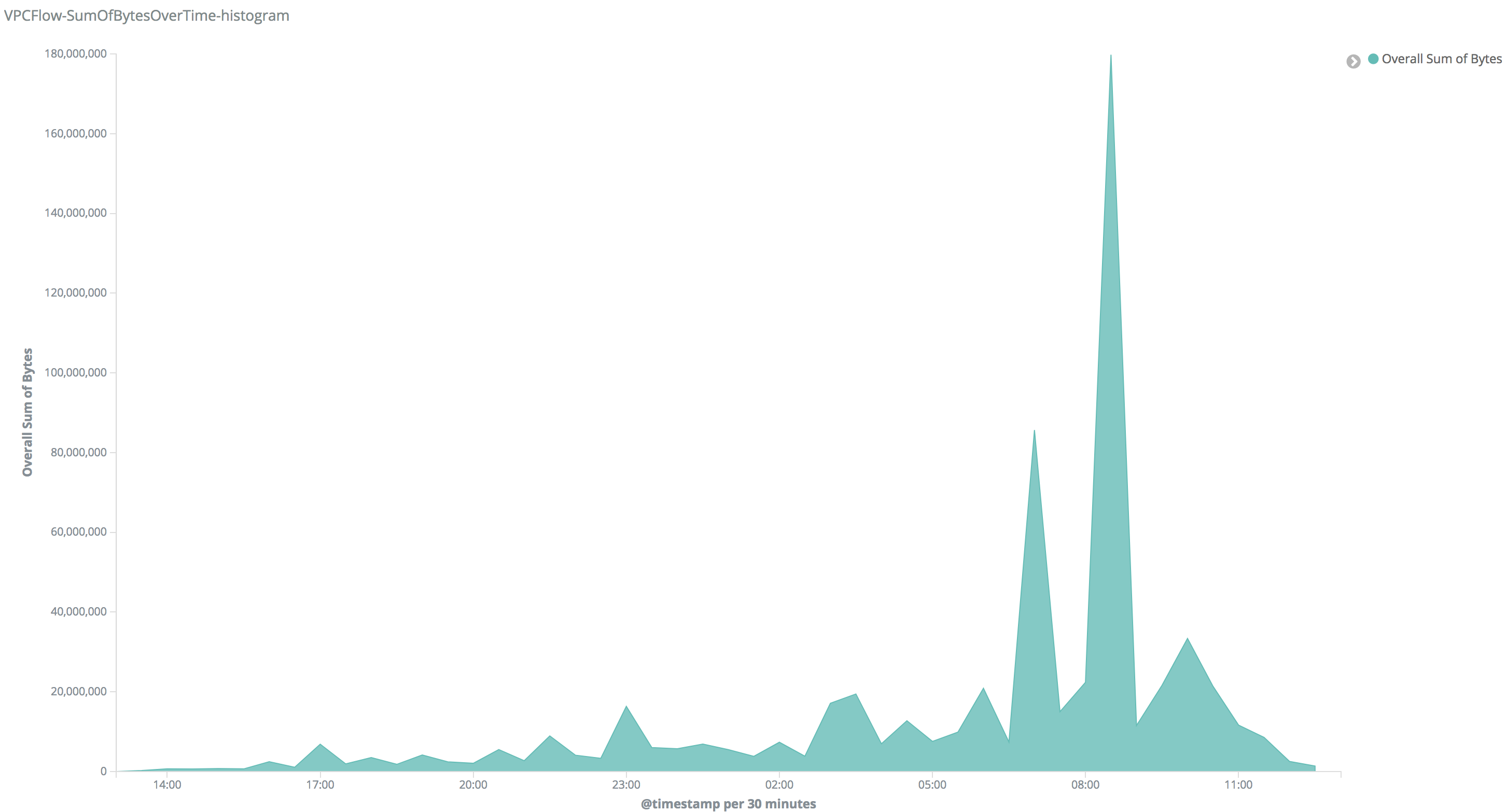
On that visualization you can look for peaks in your network, once you found a peak you can filter the alerts generated on that time and check which IPs were communicating. Since IP address is a field used in many AWS alerts, you'll probably found other alerts and find out what happened.