Google Workspace
Google Workspace, developed and marketed by Google, is a collection of cloud computing, productivity, and collaboration tools. In this guide, we integrate Google IdP to authenticate users into the Wazuh platform.
Learn how to create administrator and read-only roles on Google Workspace and map them with Wazuh in the sections below.
Setup Google Workspace single sign-on with administrator role
Follow these steps to integrate Google Workspace IdP with Wazuh for single sign-on and grant administrator role to the authenticated Google Workspace users on the Wazuh platform:
Google Workspace Configuration
Create an account in Google Workspace. A Google Workspace account is required for this configuration. Request a free trial if you don't have a paid license.
Go to https://admin.google.com/ac/apps/unified and sign in with your Google Admin account.
Create an app with Add custom SAML app.
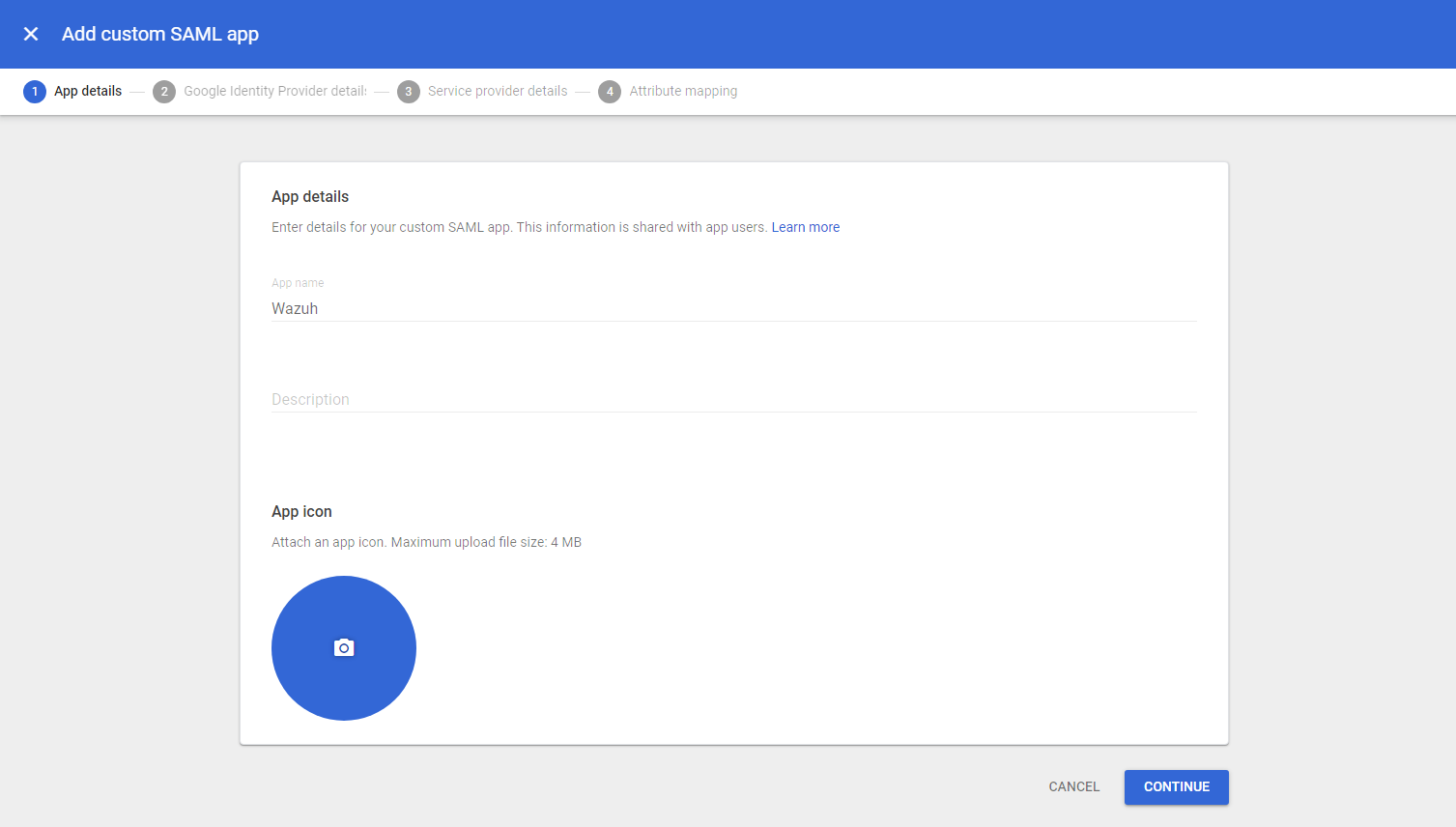
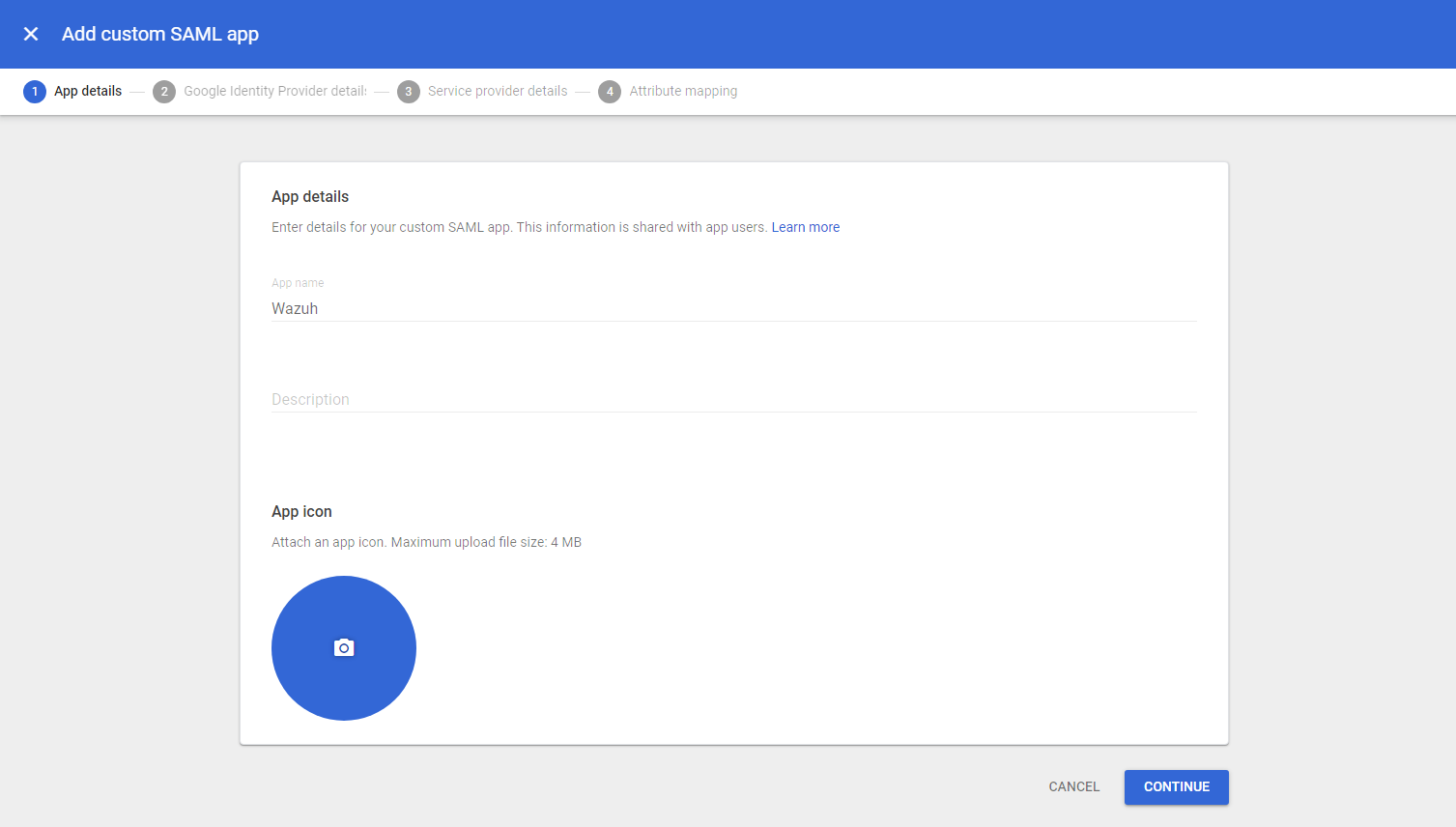
Go to Apps > Web and mobile apps > Add App, then Add custom SAML app. Enter an App name and click CONTINUE.
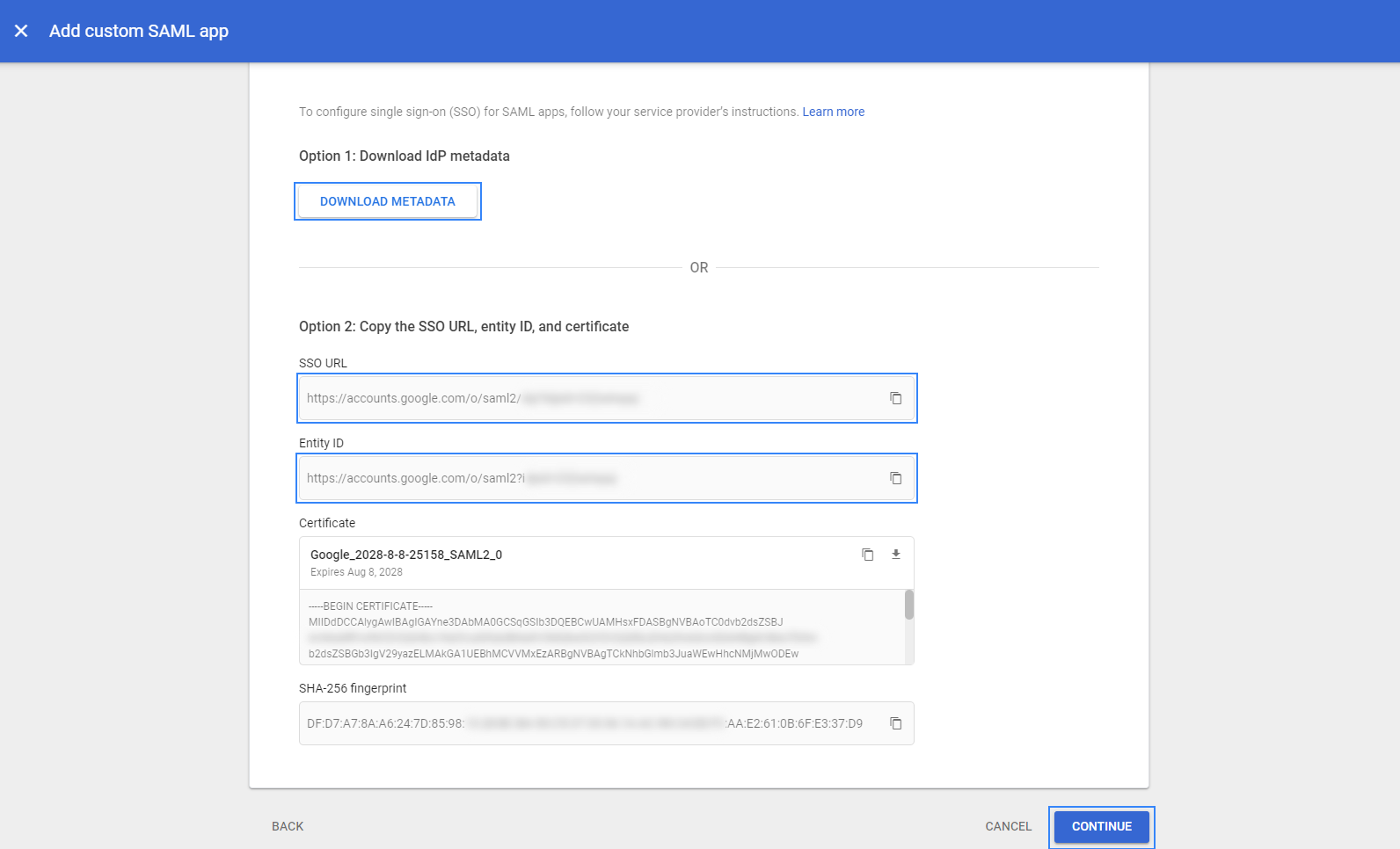
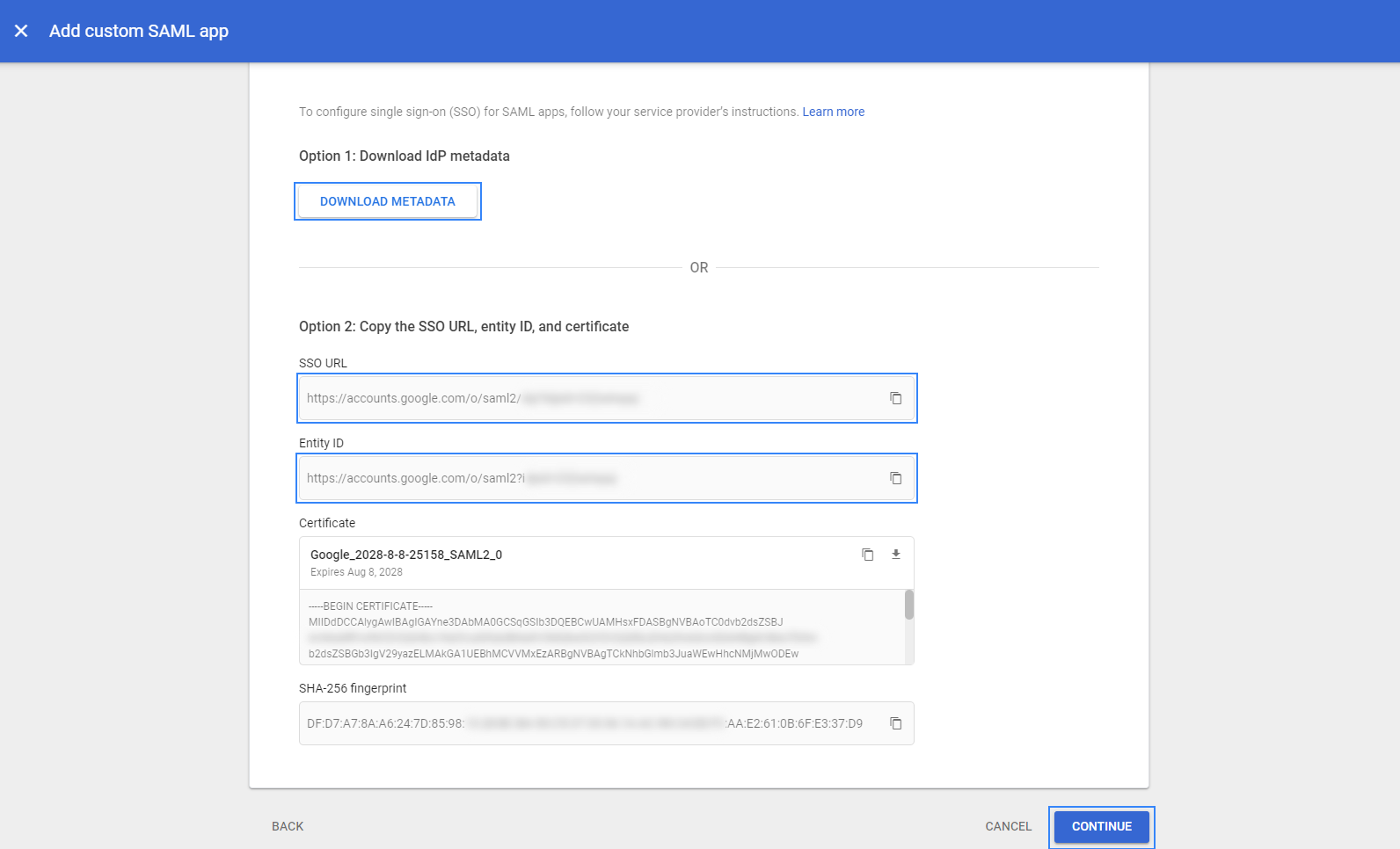
Take note of the following parameters, as they will be used during the Wazuh indexer configuration:
Entity ID: This will be used later as the
idp.entity_idSelect DOWNLOAD METADATA and place the metadata file in the
configurationdirectory of the Wazuh indexer. The path to the directory is/etc/wazuh-indexer/opensearch-security/.
Select CONTINUE and configure the following:
ACS URL:
https://<WAZUH_DASHBOARD_URL>/_opendistro/_security/saml/acs. Replace the Wazuh dashboard URL field with the appropriate URL or IP address.Entity ID: Use any name here. This will be the
sp.entity_idin the Wazuh indexer configuration file. In our case, the value iswazuh-saml.
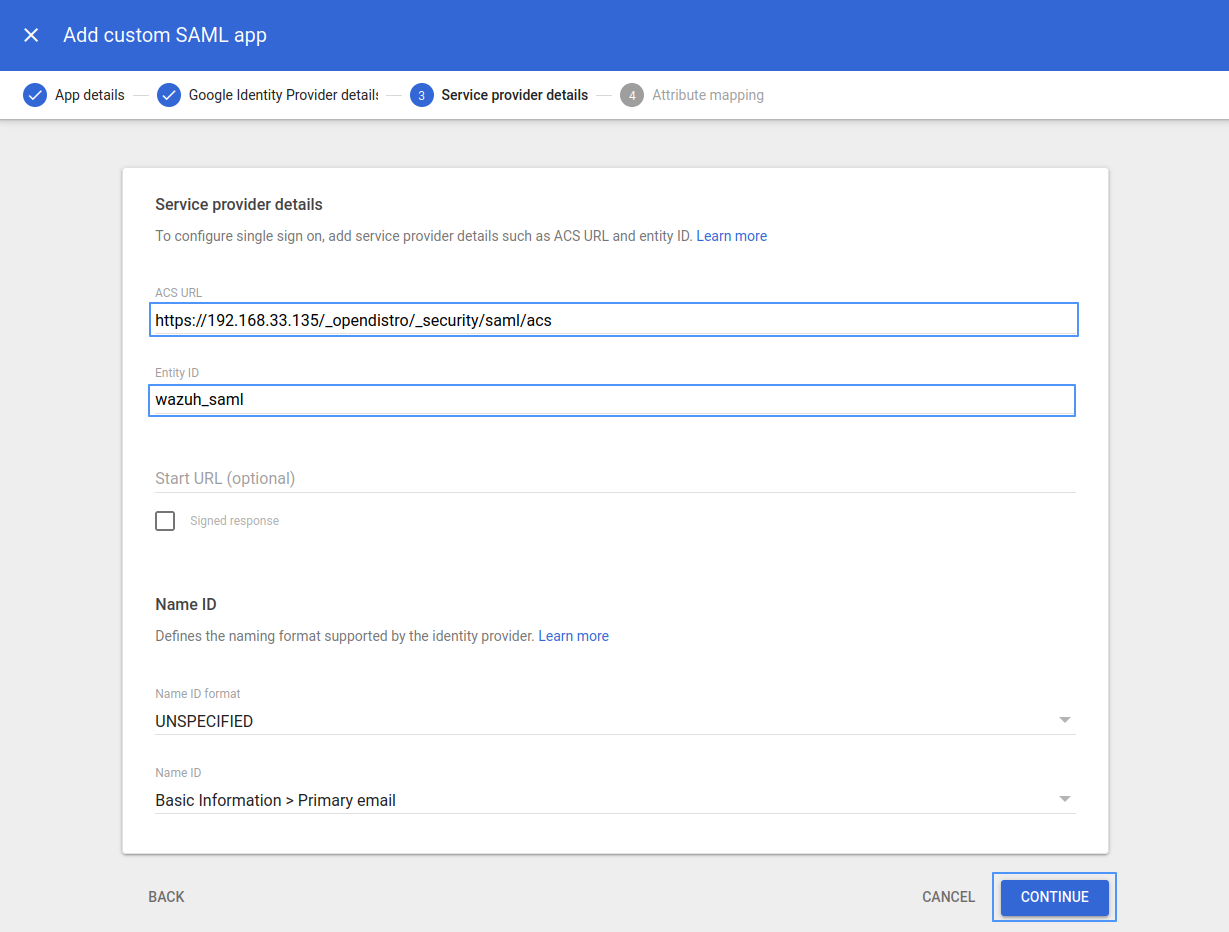
Leave the remaining parameters with their default values, then select CONTINUE.
Click on ADD MAPPING, under Employee details, choose Department, under App attributes, type Roles, and click FINISH.
Google doesn't support sending the Group membership attribute as part of the SAML Assertion (as the other Identity Providers do). So in this example, we are going to use Department as the attribute whose value will be used as our
roles_keyin the Wazuh indexer configuration. In this case, the value for the Department attribute will be stored asRoles.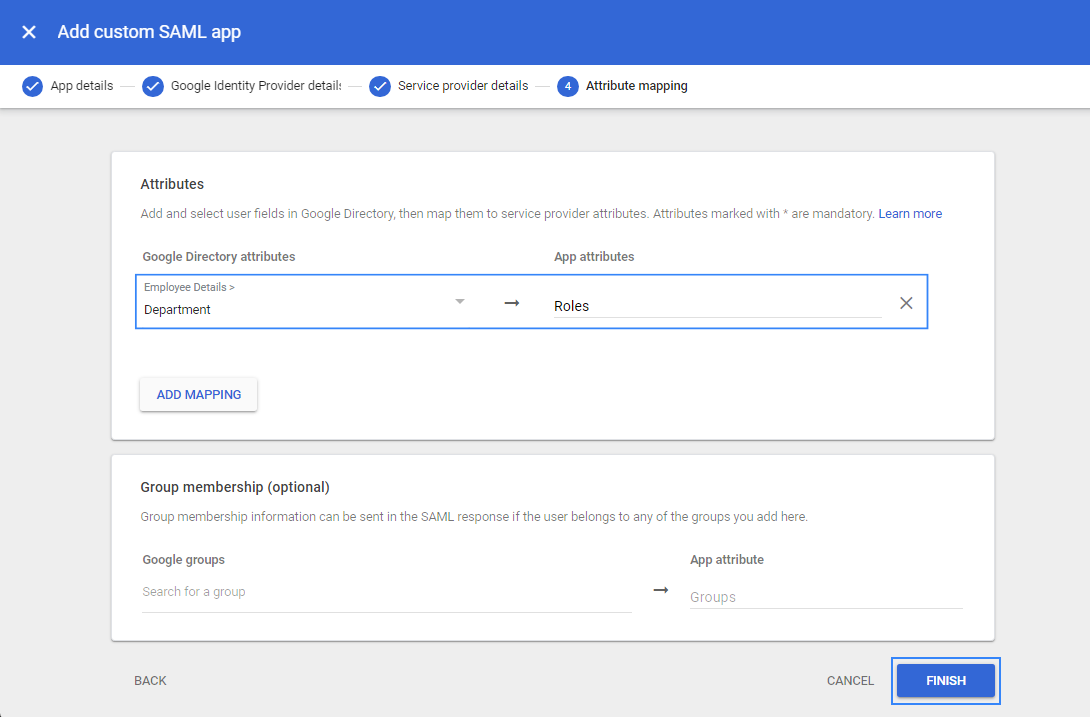
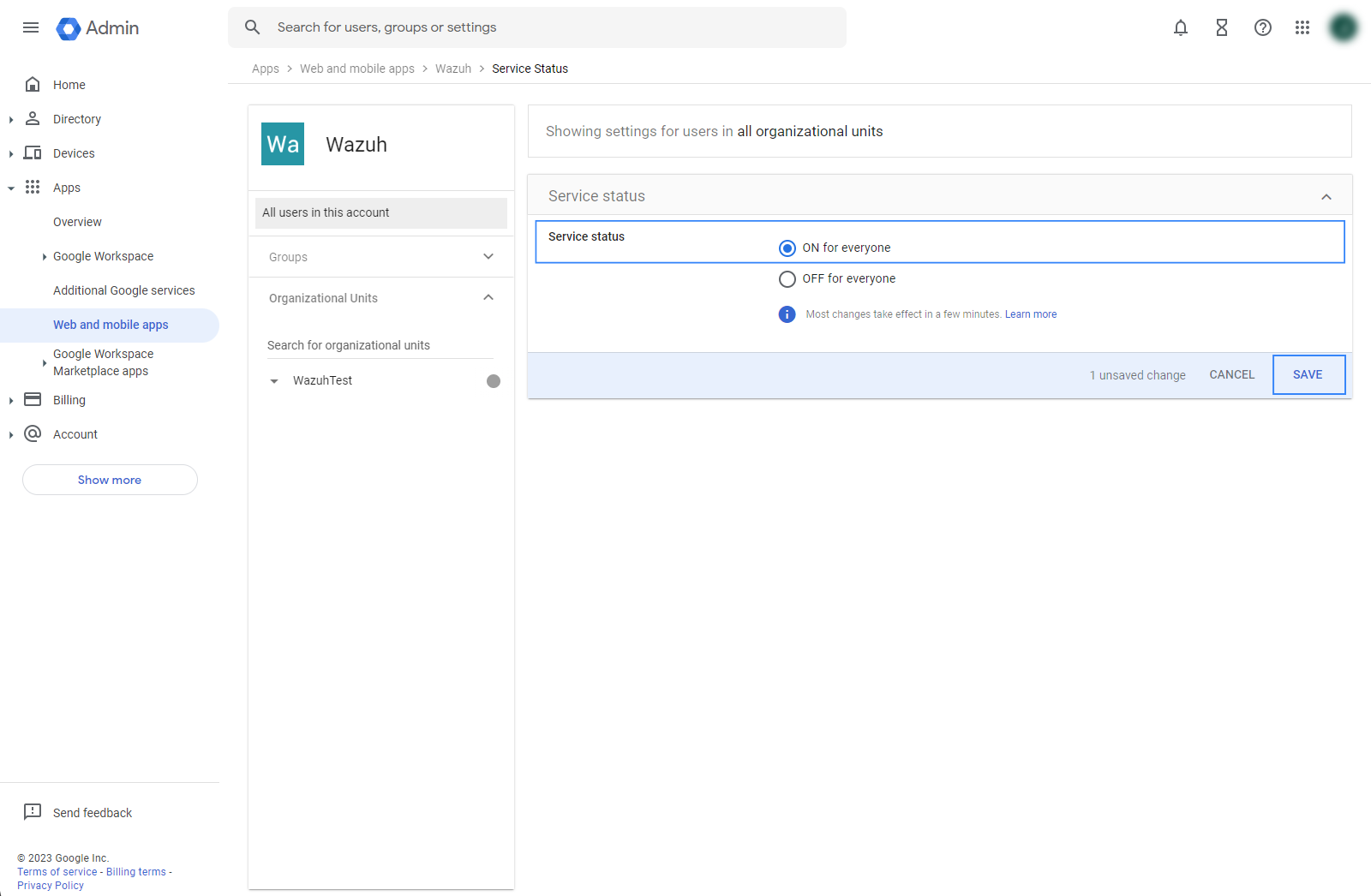
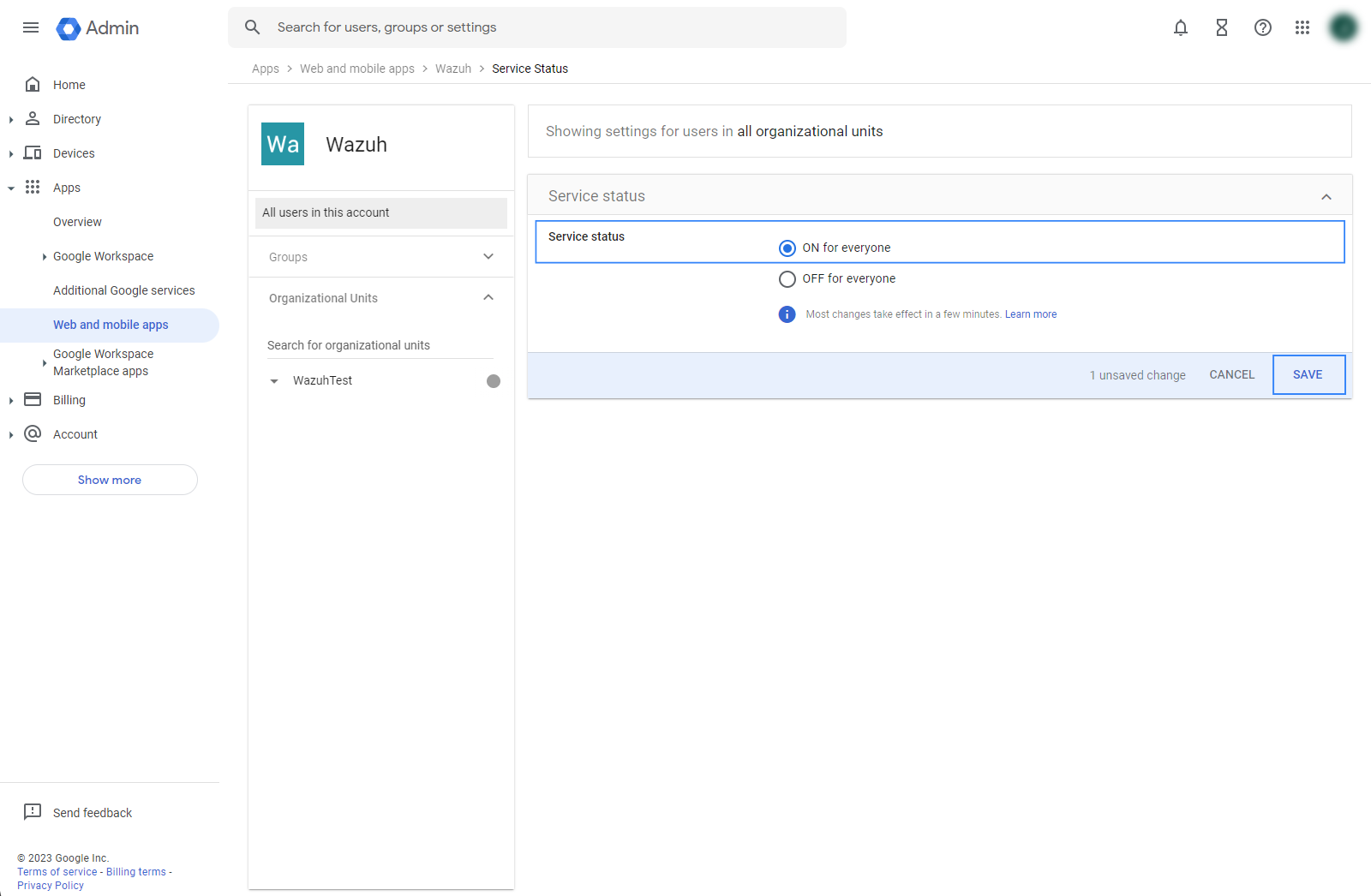
Turn ON access for everyone.
Select the recently created app and click on User access.
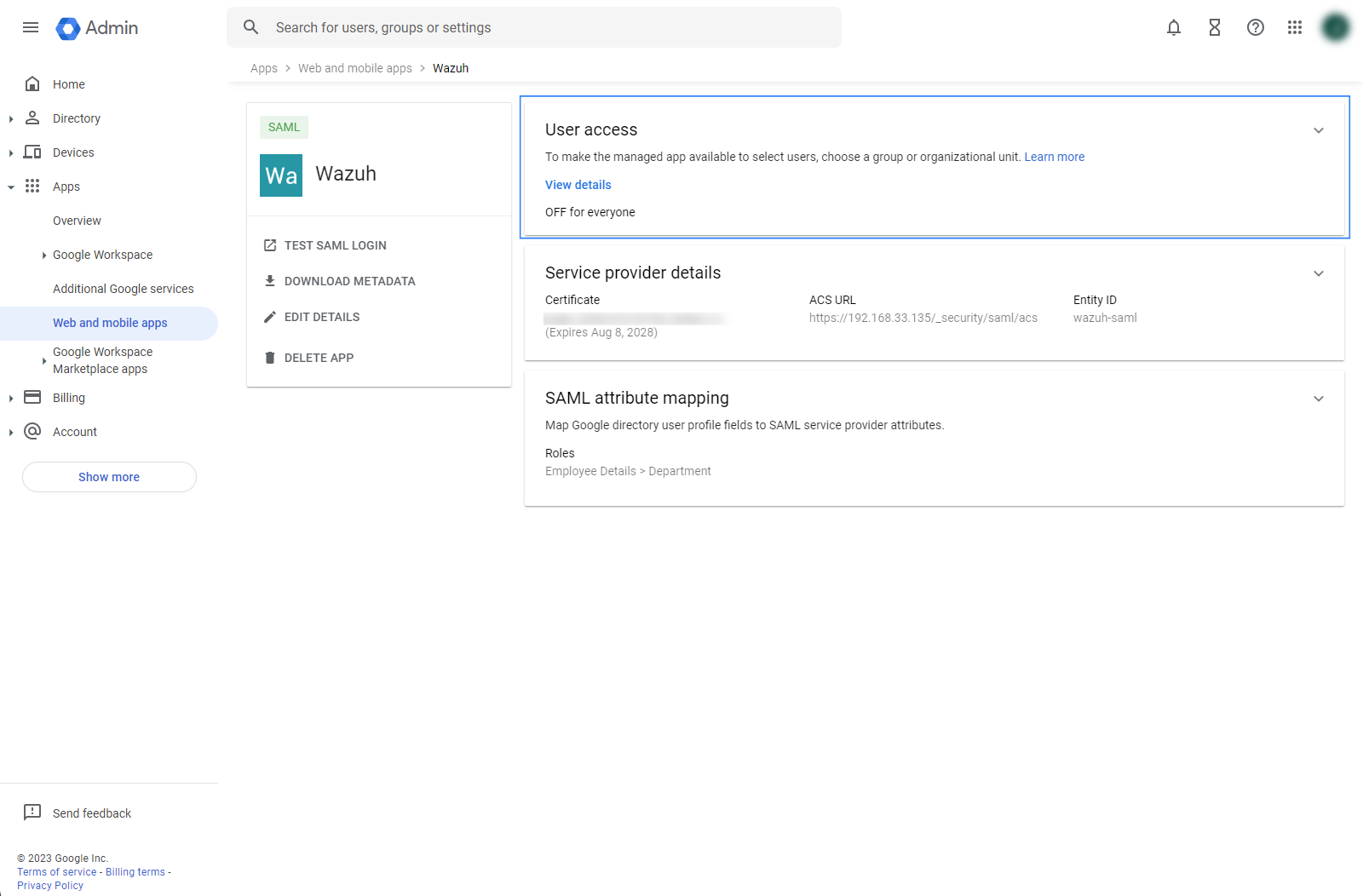
Select ON for everyone and click SAVE.
Define the attribute for users.
Go to Directory then Users.
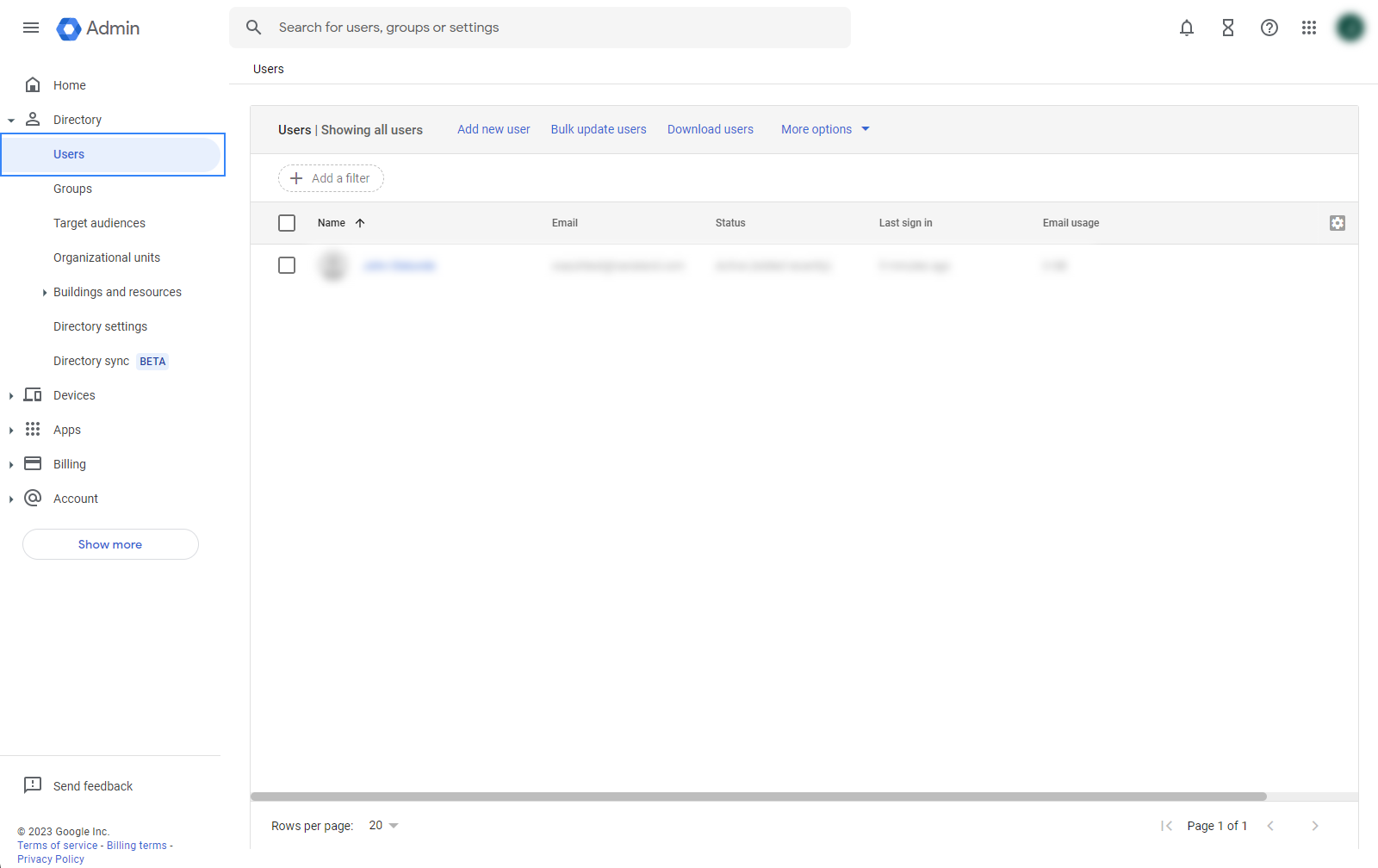
Select a user, go to User information, then edit Employee information.
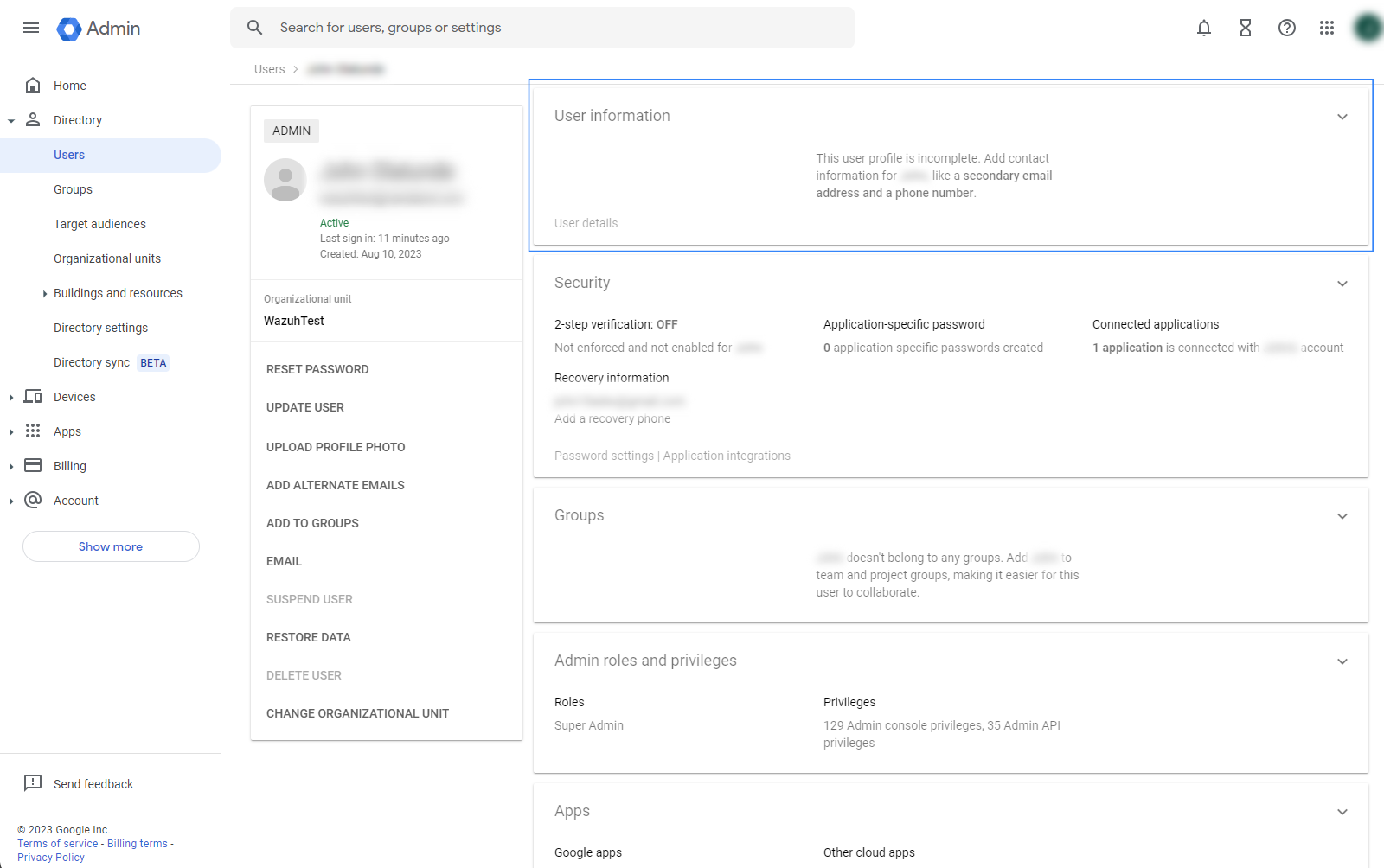
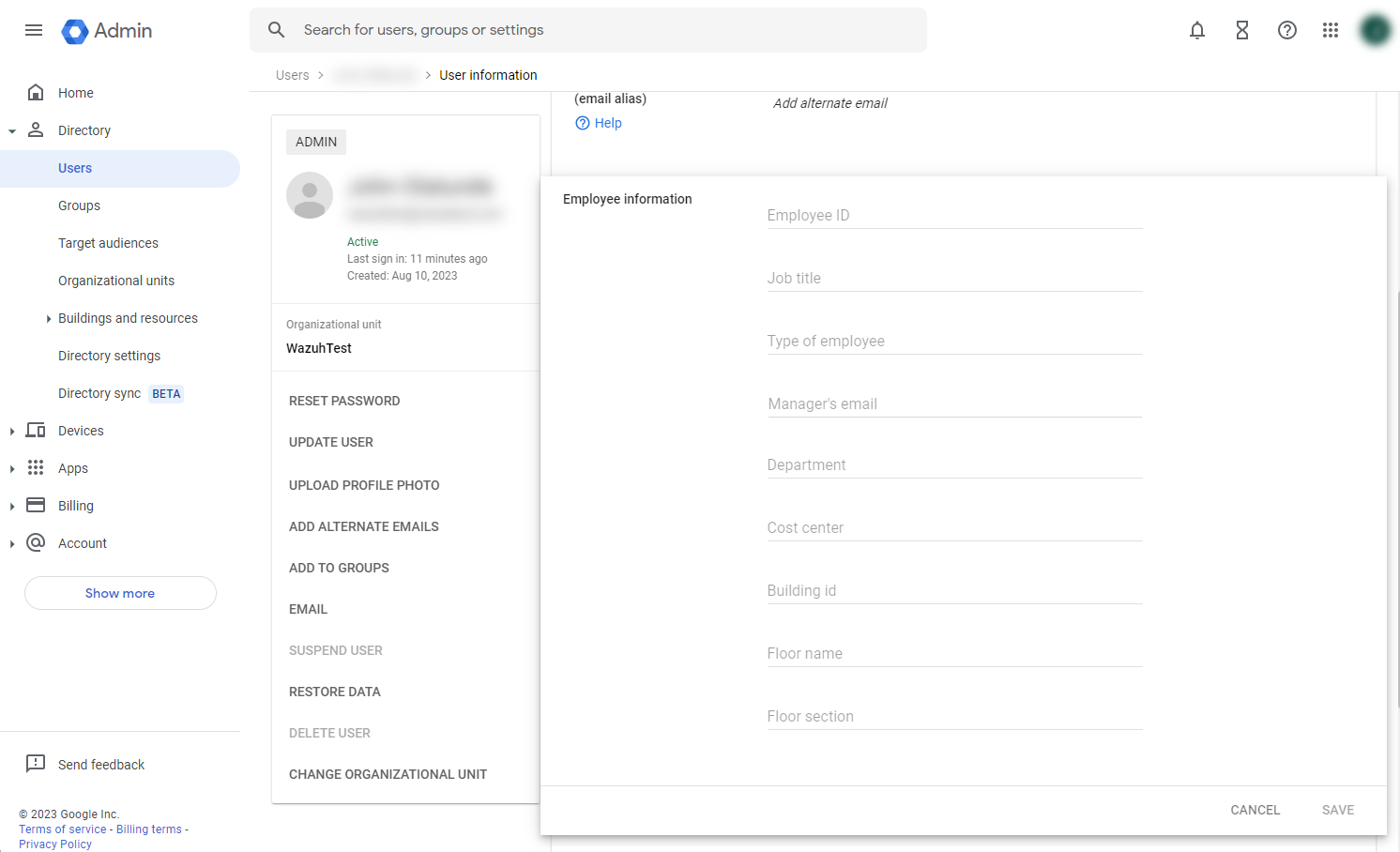
Add a value to the Department field, in this example, we add
Wazuh_access, click on SAVE. This value will be used in therole_mappingfile configuration.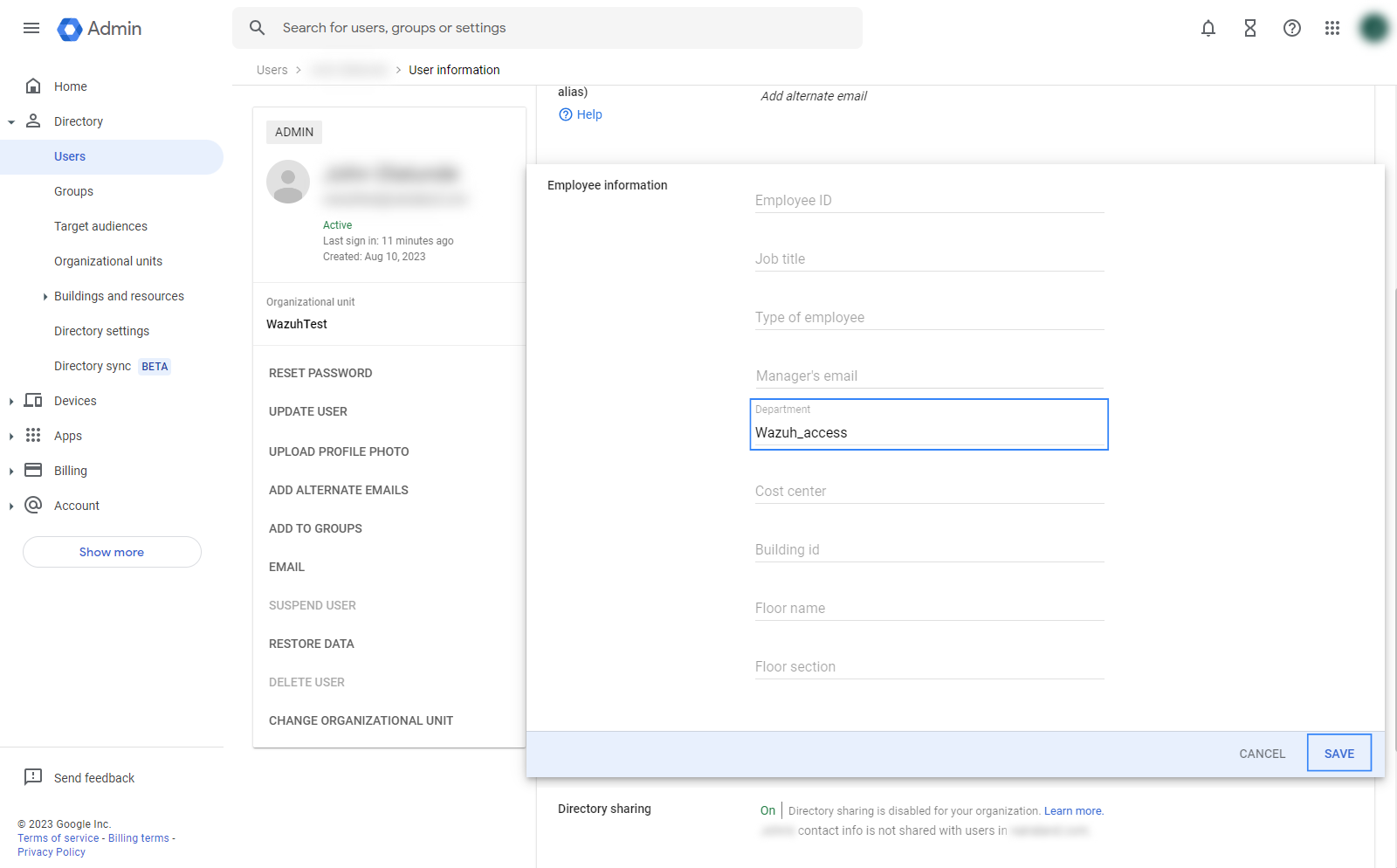
Wazuh indexer configuration
Edit the Wazuh indexer security configuration files. We recommend that you back up these files before you carry out the configuration.
Backup the existing Wazuh indexer security configuration files:
# /usr/share/wazuh-indexer/bin/indexer-security-init.sh --options "-backup /etc/wazuh-indexer/opensearch-security -icl -nhnv"
Generate a 64-character long random key using the following command.
openssl rand -hex 32The output will be used as the
exchange_keyin the/etc/wazuh-indexer/opensearch-security/config.ymlfile.Place the
Google_Metadata.xmlfile within the/etc/wazuh-indexer/opensearch-security/directory. Set the file ownership towazuh-indexerusing the following command:# chown wazuh-indexer:wazuh-indexer /etc/wazuh-indexer/opensearch-security/Google_Metadata.xml
Edit the
/etc/wazuh-indexer/opensearch-security/config.ymlfile and change the following values:Set the
orderinbasic_internal_auth_domainto0and thechallengeflag tofalse.Include a
saml_auth_domainconfiguration under theauthcsection similar to the following:
authc: ... basic_internal_auth_domain: description: "Authenticate via HTTP Basic against internal users database" http_enabled: true transport_enabled: true order: 0 http_authenticator: type: "basic" challenge: false authentication_backend: type: "intern" saml_auth_domain: http_enabled: true transport_enabled: false order: 1 http_authenticator: type: saml challenge: true config: idp: metadata_file: '/etc/wazuh-indexer/opensearch-security/Google_Metadata.xml' entity_id: 'https://accounts.google.com/o/saml2?idpid=C02…' sp: entity_id: wazuh-saml kibana_url: https://<WAZUH_DASHBOARD_URL> roles_key: Roles exchange_key: 'b1d6dd32753374557dcf92e241.......' authentication_backend: type: noop
Ensure to change the following parameters to their corresponding value:
idp.metadata_fileidp.entity_idsp.entity_idkibana_urlroles_keyexchange_key
Run the
securityadminscript to load the configuration changes made in theconfig.ymlfile.# export JAVA_HOME=/usr/share/wazuh-indexer/jdk/ && bash /usr/share/wazuh-indexer/plugins/opensearch-security/tools/securityadmin.sh -f /etc/wazuh-indexer/opensearch-security/config.yml -icl -key /etc/wazuh-indexer/certs/admin-key.pem -cert /etc/wazuh-indexer/certs/admin.pem -cacert /etc/wazuh-indexer/certs/root-ca.pem -h localhost -nhnv
The
-hflag specifies the hostname or the IP address of the Wazuh indexer node. Note that this command uses localhost, set your Wazuh indexer address if necessary.The command output must be similar to the following:
Security Admin v7 Will connect to localhost:9200 ... done Connected as "CN=admin,OU=Wazuh,O=Wazuh,L=California,C=US" OpenSearch Version: 2.19.4 Contacting opensearch cluster 'opensearch' and wait for YELLOW clusterstate ... Clustername: wazuh-cluster Clusterstate: GREEN Number of nodes: 1 Number of data nodes: 1 .opendistro_security index already exists, so we do not need to create one. Populate config from /home/wazuh-user Will update '/config' with /etc/wazuh-indexer/opensearch-security/config.yml SUCC: Configuration for 'config' created or updated SUCC: Expected 1 config types for node {"updated_config_types":["config"],"updated_config_size":1,"message":null} is 1 (["config"]) due to: null Done with success
Edit the
/etc/wazuh-indexer/opensearch-security/roles_mapping.ymlfile and change the following values:Map the
Departmentfield value that was obtained in Google IdP to theall_accessrole in the Wazuh indexer:all_access: reserved: false hidden: false backend_roles: - "admin" - "Wazuh_access" description: "Maps admin and Wazuh_access to all_access"
Run the
securityadminscript to load the configuration changes made in theroles_mapping.ymlfile.# export JAVA_HOME=/usr/share/wazuh-indexer/jdk/ && bash /usr/share/wazuh-indexer/plugins/opensearch-security/tools/securityadmin.sh -f /etc/wazuh-indexer/opensearch-security/roles_mapping.yml -icl -key /etc/wazuh-indexer/certs/admin-key.pem -cert /etc/wazuh-indexer/certs/admin.pem -cacert /etc/wazuh-indexer/certs/root-ca.pem -h localhost -nhnv
The
-hflag specifies the hostname or the IP address of the Wazuh indexer node. Note that this command uses localhost, set your Wazuh indexer address if necessary.The command output must be similar to the following:
Security Admin v7 Will connect to localhost:9200 ... done Connected as "CN=admin,OU=Wazuh,O=Wazuh,L=California,C=US" OpenSearch Version: 2.19.4 Contacting opensearch cluster 'opensearch' and wait for YELLOW clusterstate ... Clustername: wazuh-cluster Clusterstate: GREEN Number of nodes: 1 Number of data nodes: 1 .opendistro_security index already exists, so we do not need to create one. Populate config from /home/wazuh-user Will update '/rolesmapping' with /etc/wazuh-indexer/opensearch-security/roles_mapping.yml SUCC: Configuration for 'rolesmapping' created or updated SUCC: Expected 1 config types for node {"updated_config_types":["rolesmapping"],"updated_config_size":1,"message":null} is 1 (["rolesmapping"]) due to: null Done with success
Wazuh dashboard configuration
Verify that
run_asis set totruein the/usr/share/wazuh-dashboard/data/wazuh/config/wazuh.ymlconfiguration file. This is required to create a role mapping in the Wazuh dashboard, ensuring the backend role provided by the IdP is correctly mapped to the corresponding Wazuh role.hosts: - default: url: https://localhost port: 55000 username: wazuh-wui password: "<WAZUH_WUI_PASSWORD>" run_as: true
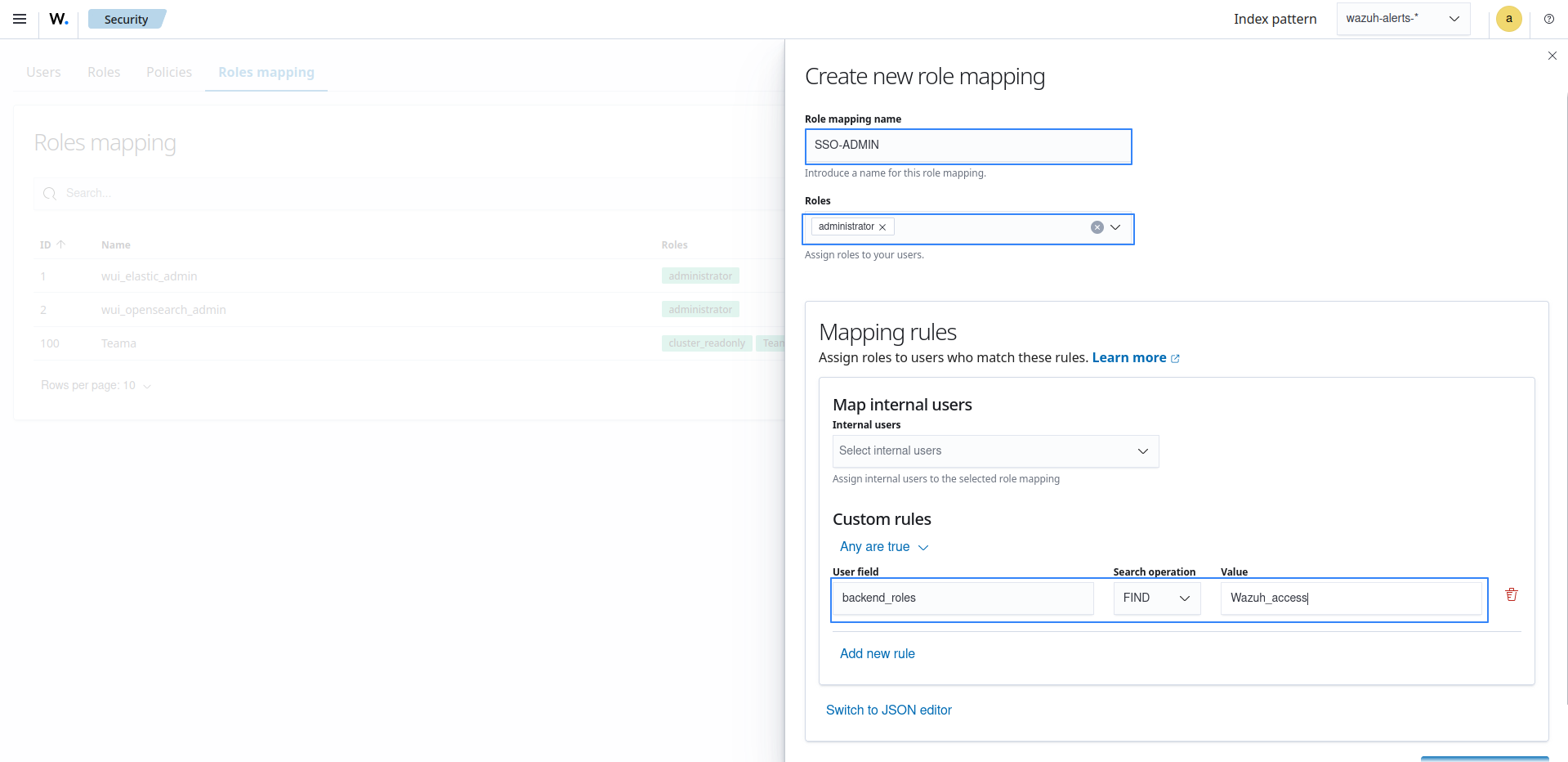
Click ☰ to open the menu on the Wazuh dashboard, go to Server management > Security, and then Roles mapping to open the page.
Click Create Role mapping and complete the empty fields with the following parameters:
Role mapping name: Assign a name to the role mapping.
Roles: Select
administrator.Custom rules: Click Add new rule to expand this field.
User field:
backend_rolesSearch operation:
FINDValue: Assign the
Departmentfield value that was obtained in Google IdP, in our case, this isWazuh_access.Click Save role mapping to save and map the backend role with Wazuh as administrator.
Edit the Wazuh dashboard configuration file. Add these configurations to
/etc/wazuh-dashboard/opensearch_dashboards.yml. We recommend that you back up these files before you carry out the configuration.opensearch_security.auth.multiple_auth_enabled: true opensearch_security.auth.type: ["basicauth","saml"] server.xsrf.allowlist: ["/_opendistro/_security/saml/acs", "/_opendistro/_security/saml/logout", "/_opendistro/_security/saml/acs/idpinitiated"]
Restart the Wazuh dashboard service using this command:
# systemctl restart wazuh-dashboard
Test the configuration. Go to your Wazuh dashboard URL and log in with your Google Workspace account.
Setup Google Workspace single sign-on with read-only role
Follow these steps to integrate Google Workspace IdP with Wazuh for single sign-on and grant read-only role to the authenticated Google Workspace users on the Wazuh platform:
Google Workspace configuration
Create an account in Google Workspace. A Google Workspace account is required for this configuration. Request a free trial if you don't have a paid license.
Go to https://admin.google.com/ac/apps/unified and sign in with your Google Admin account.
Create an app with Add custom SAML app.
Go to Apps > Web and mobile apps > Add App, then Add custom SAML app. Enter an App name and click CONTINUE.
Take note of the following parameters, as they will be used during the Wazuh indexer configuration:
Entity ID: This will be used later as the
idp.entity_idSelect DOWNLOAD METADATA and place the metadata file in the
configurationdirectory of the Wazuh indexer. The path to the directory is/etc/wazuh-indexer/opensearch-security/.
Select CONTINUE and configure the following:
ACS URL:
https://<WAZUH_DASHBOARD_URL>/_opendistro/_security/saml/acs. Replace the Wazuh dashboard URL field with the appropriate URL or IP address.Entity ID: Use any name here. This will be the
sp.entity_idin the Wazuh indexer configuration file. In our case, the value iswazuh-saml.
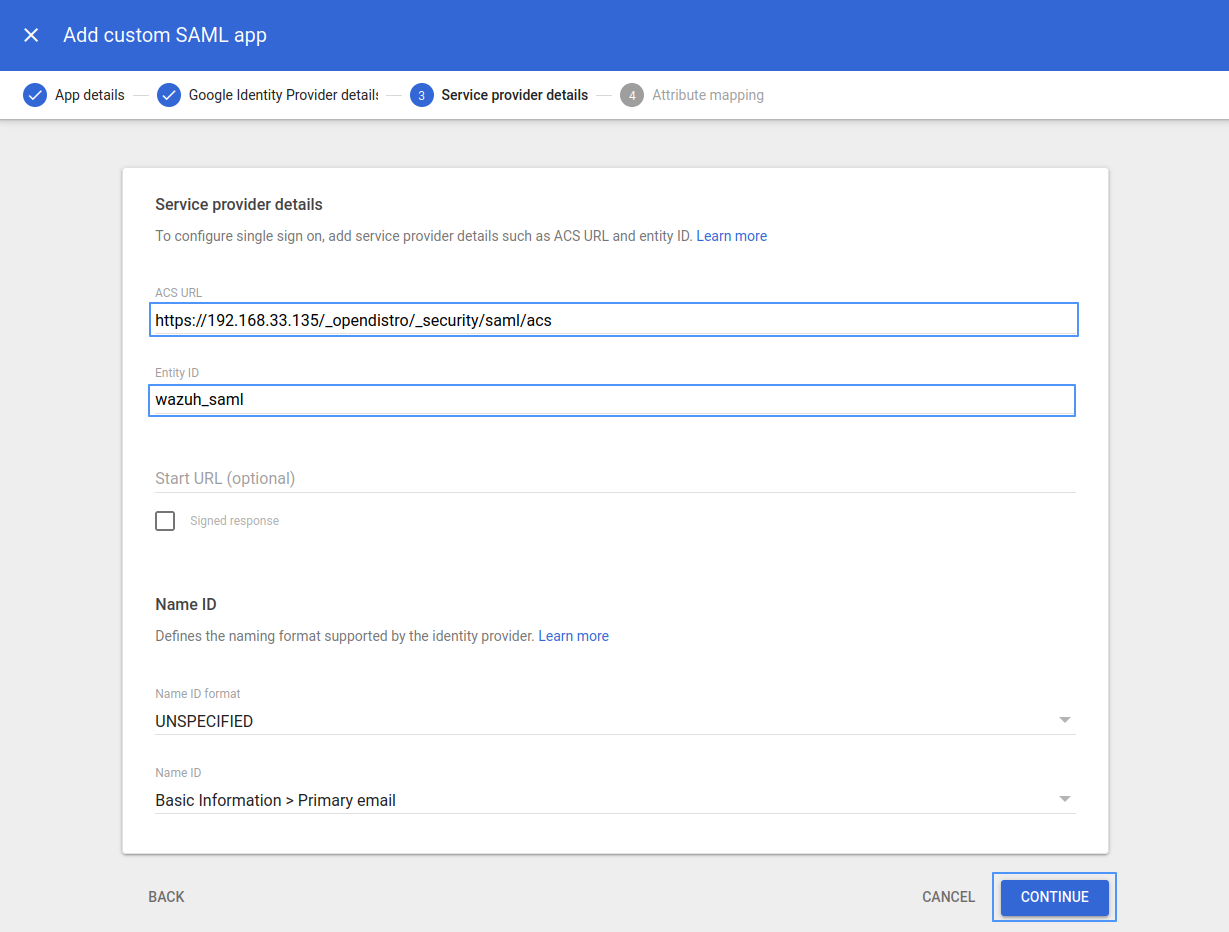
Leave the remaining parameters with their default values, then select CONTINUE.
Click on ADD MAPPING. Under Employee details, choose Department and under App attributes, type Roles. Click FINISH.
Google doesn't support sending the Group membership attribute as part of the SAML Assertion (as the other Identity Providers do). So in this example, we are going to use Department as the attribute whose value will be used as our
roles_keyin the Wazuh indexer configuration. In this case, the value for the Department attribute will be stored asRoles.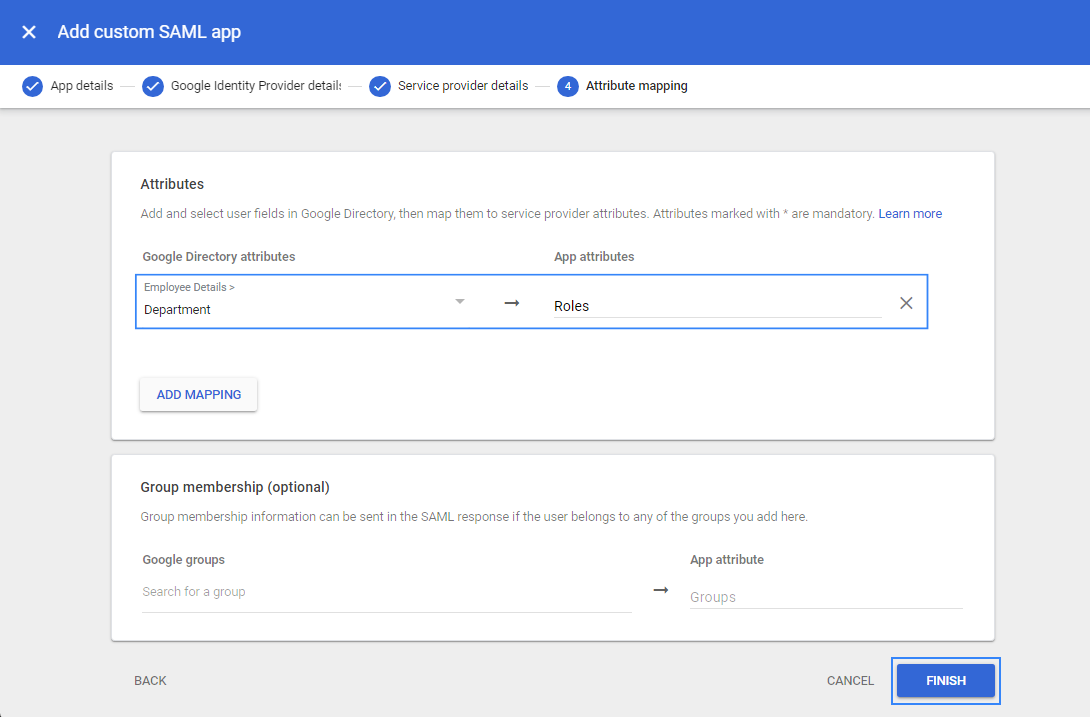
Turn ON access for everyone.
Select the recently created app and click on User access.
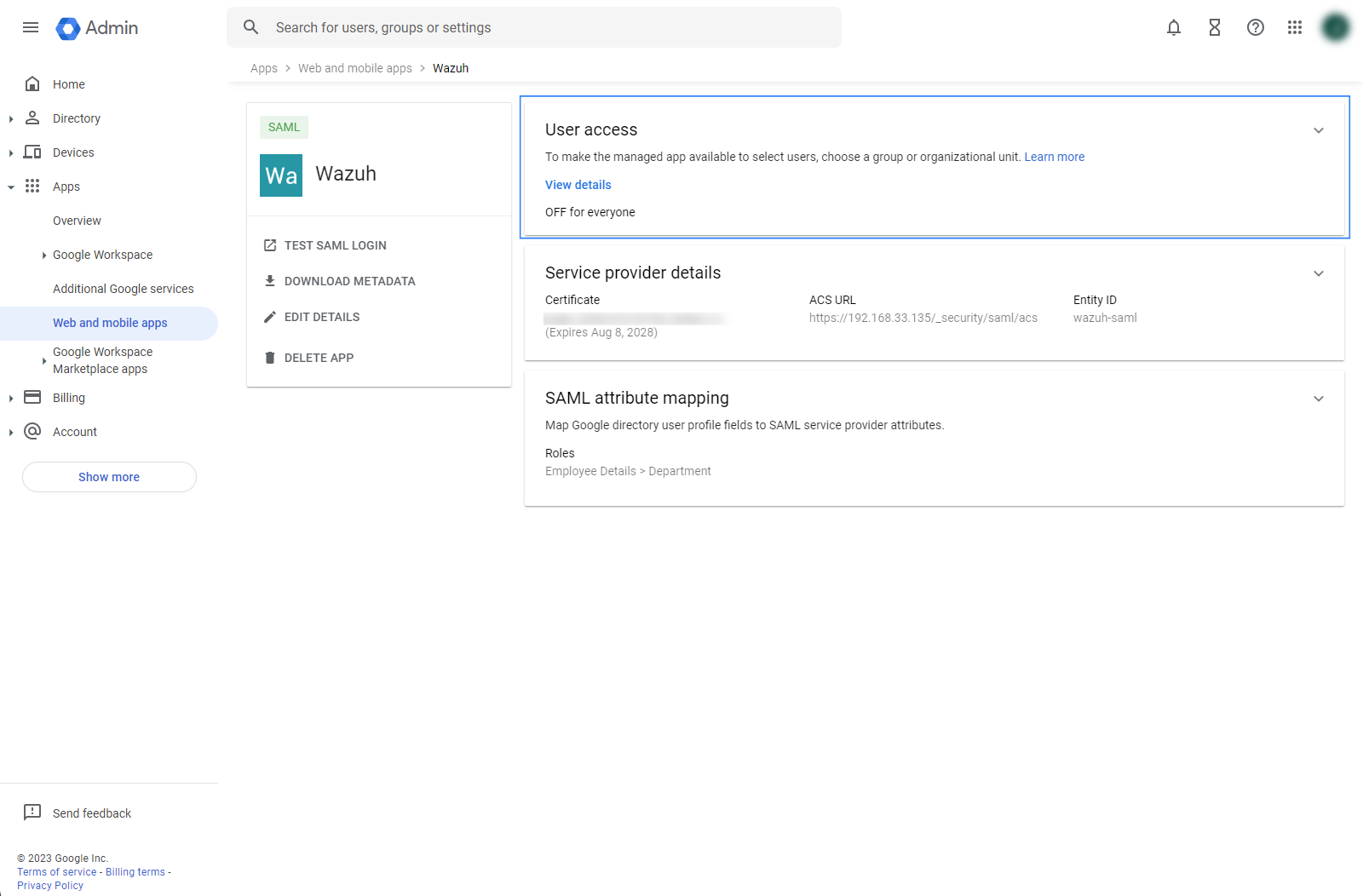
Select ON for everyone and click SAVE.
Define the attribute for users.
Go to Directory then Users.
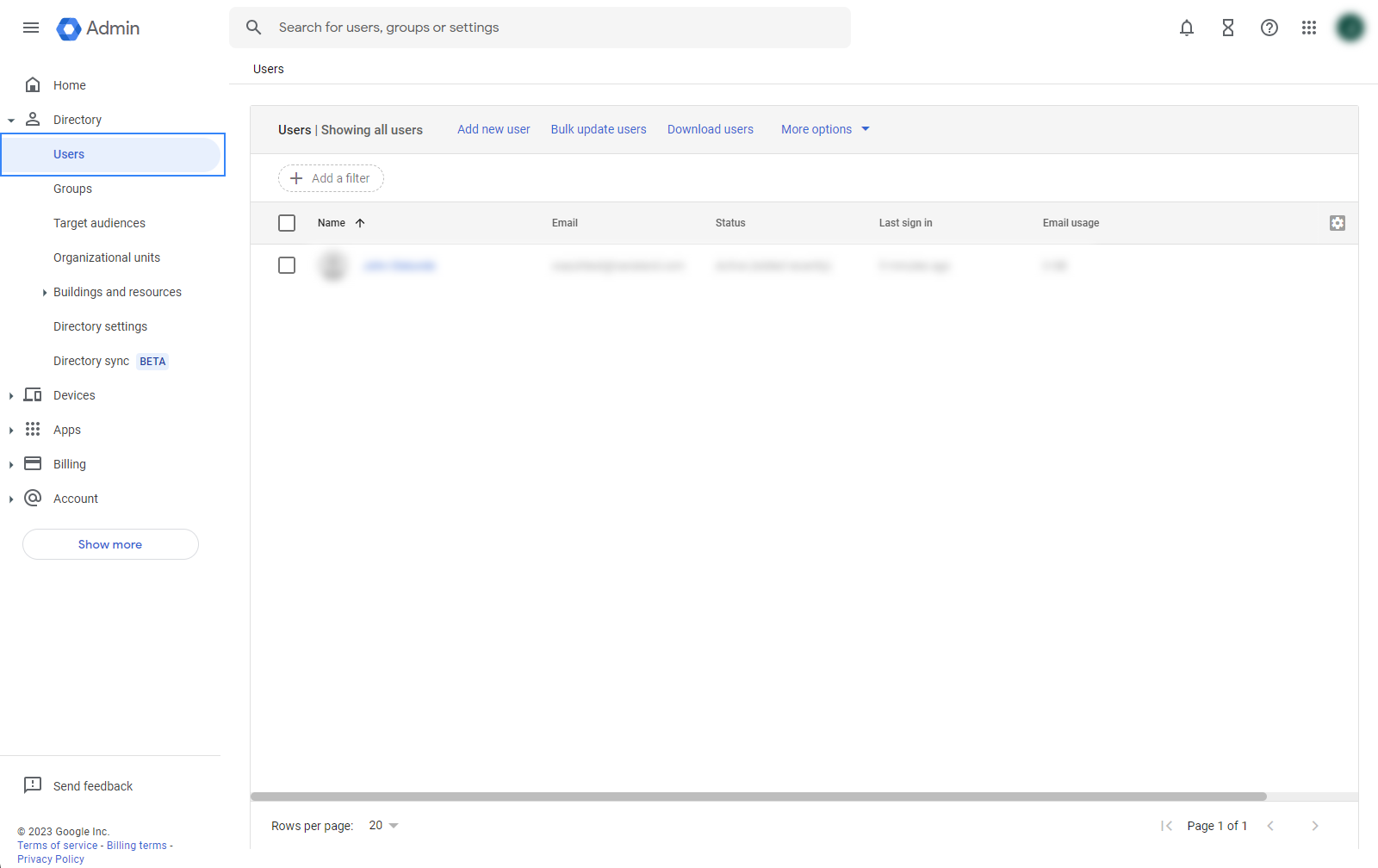
Select a user, go to User information, then edit Employee information.
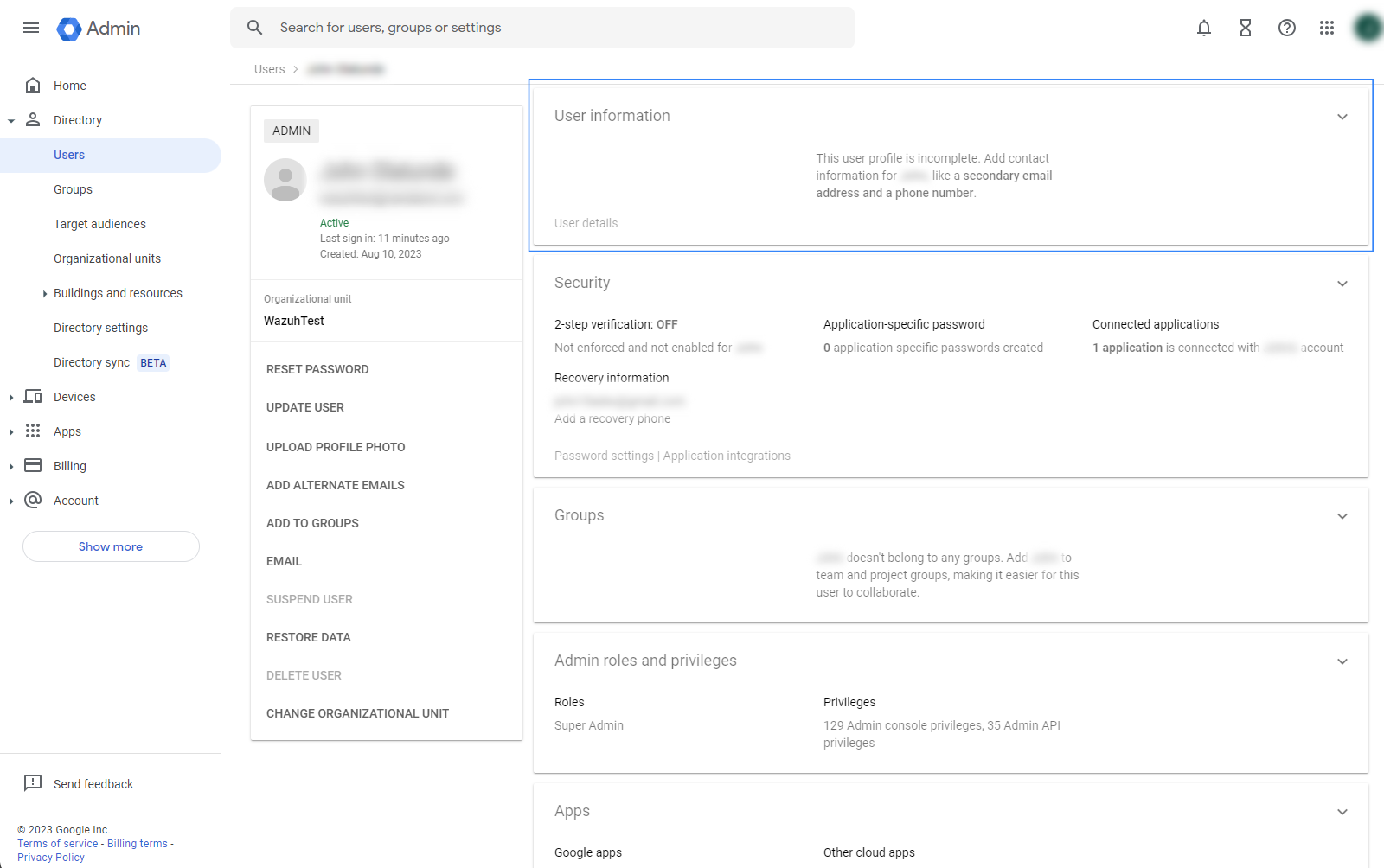
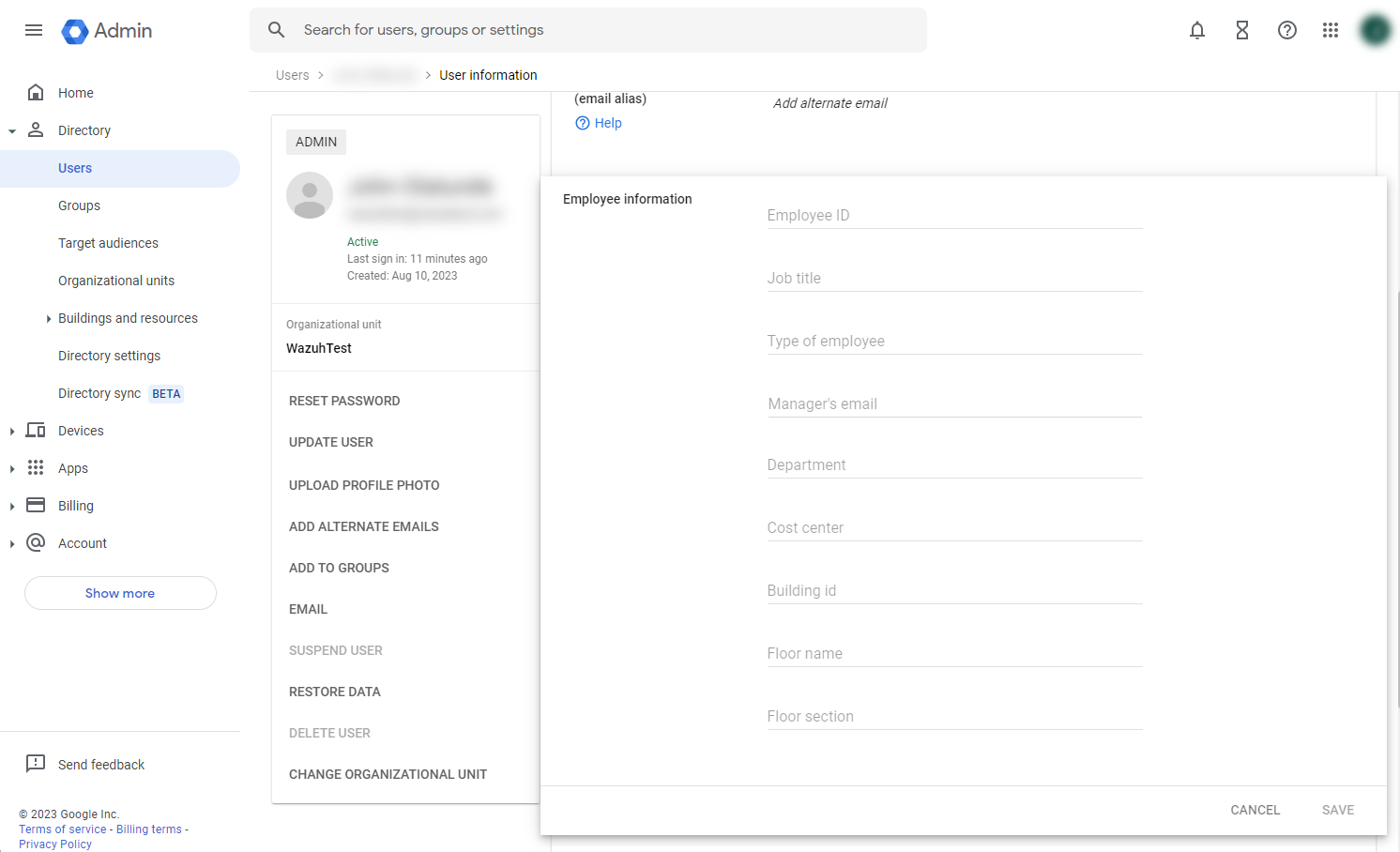
Add a value to the Department field, in this example, we add
Wazuh_access, click on SAVE. This value will be used in therole_mappingfile configuration.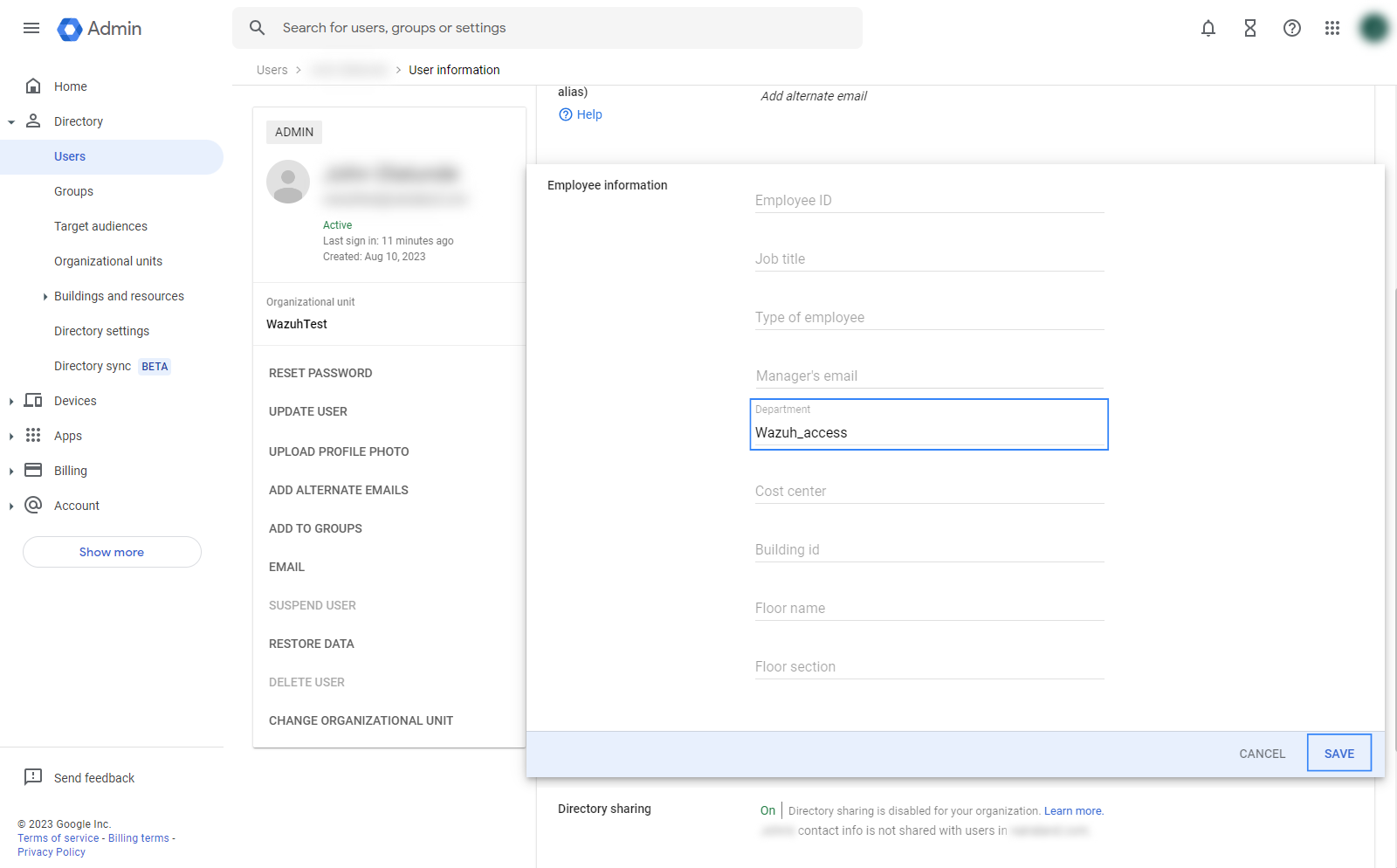
Wazuh indexer configuration
Edit the Wazuh indexer security configuration files. We recommend that you back up these files before you carry out the configuration.
Backup the existing Wazuh indexer security configuration files:
# /usr/share/wazuh-indexer/bin/indexer-security-init.sh --options "-backup /etc/wazuh-indexer/opensearch-security -icl -nhnv"
Generate a 64-character long random key using the following command.
openssl rand -hex 32The output will be used as the
exchange_keyin the/etc/wazuh-indexer/opensearch-security/config.ymlfile.Place the
Google_Metadata.xmlfile within the/etc/wazuh-indexer/opensearch-security/directory. Set the file ownership towazuh-indexerusing the following command:# chown wazuh-indexer:wazuh-indexer /etc/wazuh-indexer/opensearch-security/Google_Metadata.xml
Edit the
/etc/wazuh-indexer/opensearch-security/config.ymlfile and change the following values:Set the
orderinbasic_internal_auth_domainto0and thechallengeflag tofalse.Include a
saml_auth_domainconfiguration under theauthcsection similar to the following:
authc: ... basic_internal_auth_domain: description: "Authenticate via HTTP Basic against internal users database" http_enabled: true transport_enabled: true order: 0 http_authenticator: type: "basic" challenge: false authentication_backend: type: "intern" saml_auth_domain: http_enabled: true transport_enabled: false order: 1 http_authenticator: type: saml challenge: true config: idp: metadata_file: '/etc/wazuh-indexer/opensearch-security/Google_Metadata.xml' entity_id: 'https://accounts.google.com/o/saml2?idpid=C02…' sp: entity_id: wazuh-saml kibana_url: https://<WAZUH_DASHBOARD_URL> roles_key: Roles exchange_key: 'b1d6dd32753374557dcf92e241.......' authentication_backend: type: noop
Ensure to change the following parameters to their corresponding value:
idp.metadata_fileidp.entity_idsp.entity_idkibana_urlroles_keyexchange_key
Run the
securityadminscript to load the configuration changes made in theconfig.ymlfile.# export JAVA_HOME=/usr/share/wazuh-indexer/jdk/ && bash /usr/share/wazuh-indexer/plugins/opensearch-security/tools/securityadmin.sh -f /etc/wazuh-indexer/opensearch-security/config.yml -icl -key /etc/wazuh-indexer/certs/admin-key.pem -cert /etc/wazuh-indexer/certs/admin.pem -cacert /etc/wazuh-indexer/certs/root-ca.pem -h localhost -nhnv
The
-hflag specifies the hostname or the IP address of the Wazuh indexer node. Note that this command uses localhost, set your Wazuh indexer address if necessary.The command output must be similar to the following:
Security Admin v7 Will connect to localhost:9200 ... done Connected as "CN=admin,OU=Wazuh,O=Wazuh,L=California,C=US" OpenSearch Version: 2.19.4 Contacting opensearch cluster 'opensearch' and wait for YELLOW clusterstate ... Clustername: wazuh-cluster Clusterstate: GREEN Number of nodes: 1 Number of data nodes: 1 .opendistro_security index already exists, so we do not need to create one. Populate config from /home/wazuh-user Will update '/config' with /etc/wazuh-indexer/opensearch-security/config.yml SUCC: Configuration for 'config' created or updated SUCC: Expected 1 config types for node {"updated_config_types":["config"],"updated_config_size":1,"message":null} is 1 (["config"]) due to: null Done with success
Wazuh dashboard configuration
Create a new role mapping for the backend role.
Follow these steps to create a new role mapping, and grant read-only permissions to the backend role.
Log into the Wazuh dashboard as administrator.
Click the upper-left menu icon ☰ to open the options, go to Indexer management > Security, and then Roles to open the roles page.
Click Create role, complete the empty fields with the following parameters, and then click Create to complete the task.
Name: Assign a name to the role.
Cluster permissions:
cluster_composite_ops_roIndex:
*Index permissions:
readTenant permissions:
global_tenantand select the Read only option.
Select the newly created role.
Select the Mapped users tab and click Manage mapping.
Under Backend roles, add the value of the Department field you created in Google Workspace and click Map to confirm the action. In our case, the backend role is
wazuh-readonly.
Verify that
run_asis set totruein the/usr/share/wazuh-dashboard/data/wazuh/config/wazuh.ymlconfiguration file. This is required to create a role mapping in the Wazuh dashboard, ensuring the backend role provided by the IdP is correctly mapped to the corresponding Wazuh role.hosts: - default: url: https://localhost port: 55000 username: wazuh-wui password: "<WAZUH_WUI_PASSWORD>" run_as: true
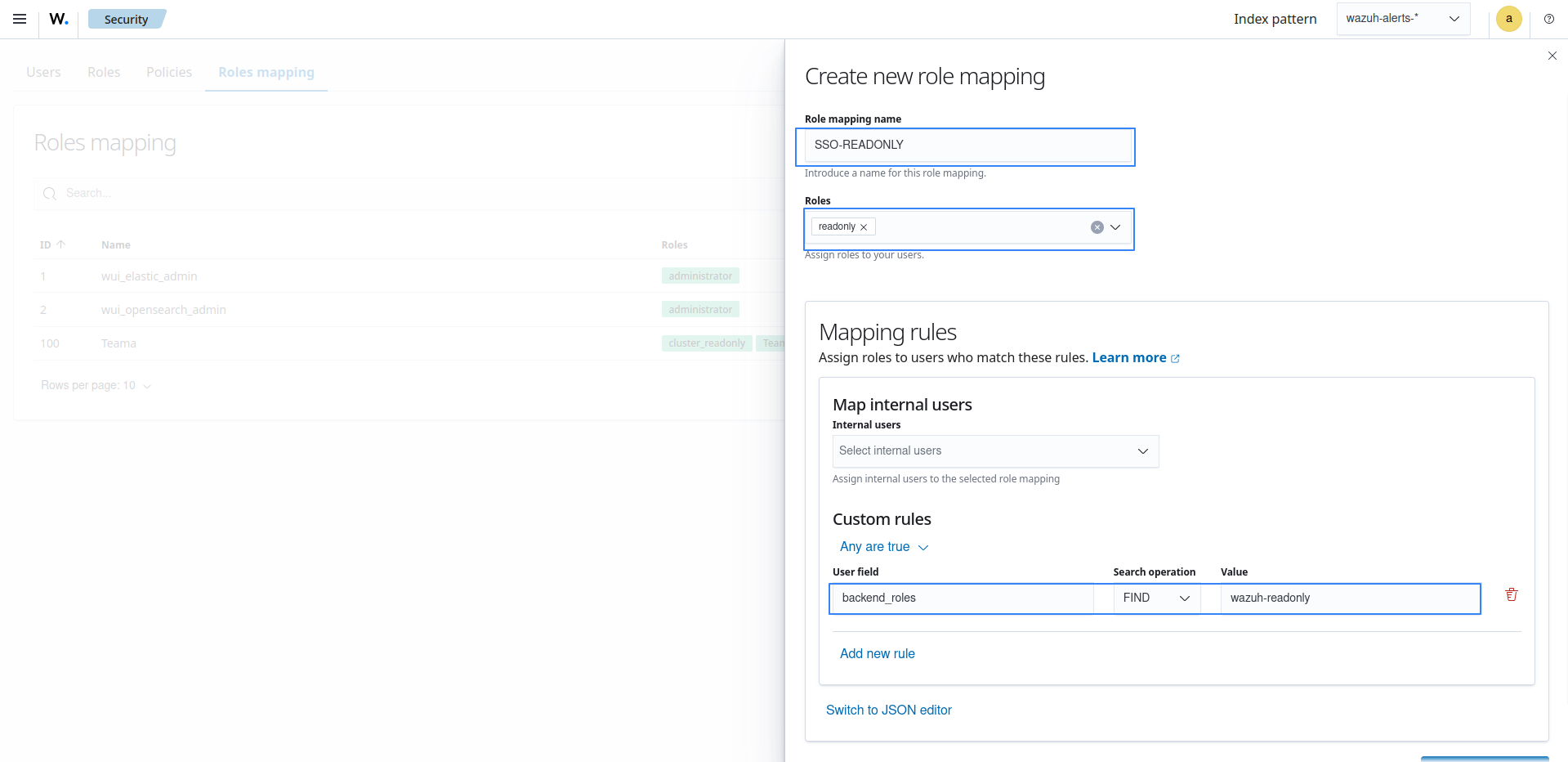
Click ☰ to open the menu on the Wazuh dashboard, go to Server management > Security, and then Roles mapping to open the page.
Click Create Role mapping and complete the empty fields with the following parameters:
Role mapping name: Assign a name to the role mapping.
Roles: Select
readonly.Custom rules: Click Add new rule to expand this field.
User field:
backend_rolesSearch operation:
FINDValue: Assign the Department field you created in Google Workspace. In our case, the backend role is
wazuh-readonly.Click Save role mapping to save and map the backend role with Wazuh as read-only.
Edit the Wazuh dashboard configuration file. Add these configurations to
/etc/wazuh-dashboard/opensearch_dashboards.yml. We recommend that you back up these files before you carry out the configuration.opensearch_security.auth.multiple_auth_enabled: true opensearch_security.auth.type: ["basicauth","saml"] server.xsrf.allowlist: ["/_opendistro/_security/saml/acs", "/_opendistro/_security/saml/logout", "/_opendistro/_security/saml/acs/idpinitiated"]
Restart the Wazuh dashboard service using this command:
# systemctl restart wazuh-dashboard
Test the configuration. To test the configuration, go to your Wazuh dashboard URL and log in with your Google Workspace account.