Malware detection
Wazuh offers several capabilities that support malware detection. These detections can be done by:
These malware detection components help meet the following PCI DSS requirement:
Requirement 5 - Protect All Systems and Networks from Malicious Software: Malicious software (malware) is software or firmware designed to infiltrate or damage a computer system without the owner's knowledge or consent, with the intent of compromising the confidentiality, integrity, or availability of the owner’s data, applications, or operating system. The goal of this requirement is to protect systems from current and evolving malware threats.
To help meet the above PCI DSS requirement, Wazuh uses a combination of rootcheck, CDB lists, integrations with VirusTotal and Yara, and active response to detect and remove malicious files.
Use cases
PCI DSS 5.2.2 requires that the deployed anti-malware solution(s):
Detects all known types of malware.
Removes, blocks, or contains all known malware types.
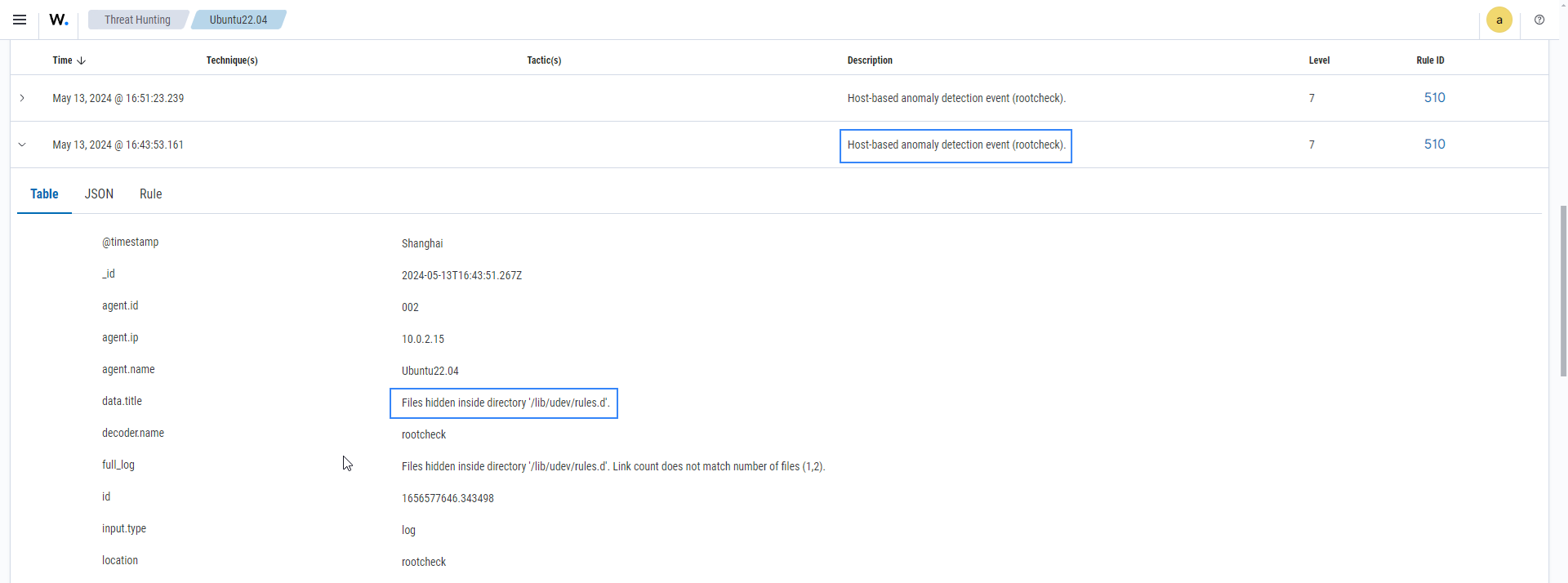
In the following example, the rootcheck module on the Ubuntu25 endpoint detects a trojaned system binary, a critical malware indicator where a legitimate system file has been replaced with a malicious version. Attackers use trojaned binaries to maintain persistence, escalate privileges, and evade detection. Wazuh rootcheck identifies this by scanning system binaries and comparing their signatures against a known set of malicious patterns, triggering rule 510 (Host-based anomaly detection event) when a match is found.
Wazuh generates an alert with rule 510, showing the full log: "Trojaned version of file
/usr/bin/md5sumdetected" when the scan runs on the monitored endpoint. This confirms that the critical system binary/usr/bin/md5sumhas been compromised, directly satisfying PCI DSS 5.2.2 by detecting a known malware type (a trojaned binary) on the endpoint.