Vulnerability detection
Wazuh can detect vulnerabilities in applications installed on agents using the Vulnerability Detector module. This module integrates vulnerability feeds from Canonical, Debian, Red Hat, Arch Linux, ALAS (Amazon Linux Advisories Security), Microsoft, and the National Vulnerability Database.
The vulnerability detection module helps to meet the following PCI DSS requirements:
Requirement 6 - Develop and Maintain Secure Systems and Software: Actors with malicious intent can exploit security vulnerabilities to gain privileged access to systems. Many of these vulnerabilities are fixed by vendor-provided security patches, which must be installed by the entities that manage the systems. All system components must have all appropriate software patches to protect against the exploitation and compromise of account data by malicious individuals and malicious software.
The goal of this requirement is to ensure that systems and software have the appropriate security patches installed to address discovered vulnerabilities and prevent compromise.
Requirement 11 - Test Security of Systems and Networks Regularly: Vulnerabilities are being discovered continually by malicious individuals and researchers, and being introduced by new software. System components, processes, and bespoke and custom software should be tested frequently to ensure security controls continue to reflect a changing environment.
The goal of this requirement is to ensure that systems and networks are regularly tested to confirm their security status. These tests include penetration testing and vulnerability scans. The Wazuh vulnerability detector module helps to meet the above requirements. The Wazuh agent runs scans on the endpoint to detect vulnerabilities. It collects a list of installed applications and OS information, and sends it to the manager periodically. The Wazuh manager compares this information with its global vulnerability database to determine what vulnerabilities exist on an endpoint. Wazuh builds this global vulnerability database from publicly available CVE repositories. You can find more details on configuring vulnerability scans in the vulnerability detection section of the documentation.
Use cases
Below are some PCI DSS requirements use cases that can be met with the vulnerability detection module:
PCI DSS 6.3 requires that security vulnerabilities be identified and addressed. You can identify these security vulnerabilities by scheduling vulnerability scans with the vulnerability scan module. In this case, we want to detect vulnerabilities in packages installed on an Ubuntu 20.04 endpoint. We add the following block to the shared agent configuration file
/var/ossec/etc/shared/default/agent.conf:<wodle name="syscollector"> <disabled>no</disabled> <interval>1h</interval> <packages>yes</packages> </wodle>
Vulnerability detection is enabled by default on a Wazuh manager. The Wazuh Vulnerability Detection module works with the Syscollector module to detect vulnerable packages and software on a monitored endpoint. You can ensure this by checking the following configuration:
<vulnerability-detection> <enabled>yes</enabled> <index-status>yes</index-status> <feed-update-interval>60m</feed-update-interval> </vulnerability-detection>
Use the following guide to ensure your Wazuh Vulnerability Detection is configured correctly.
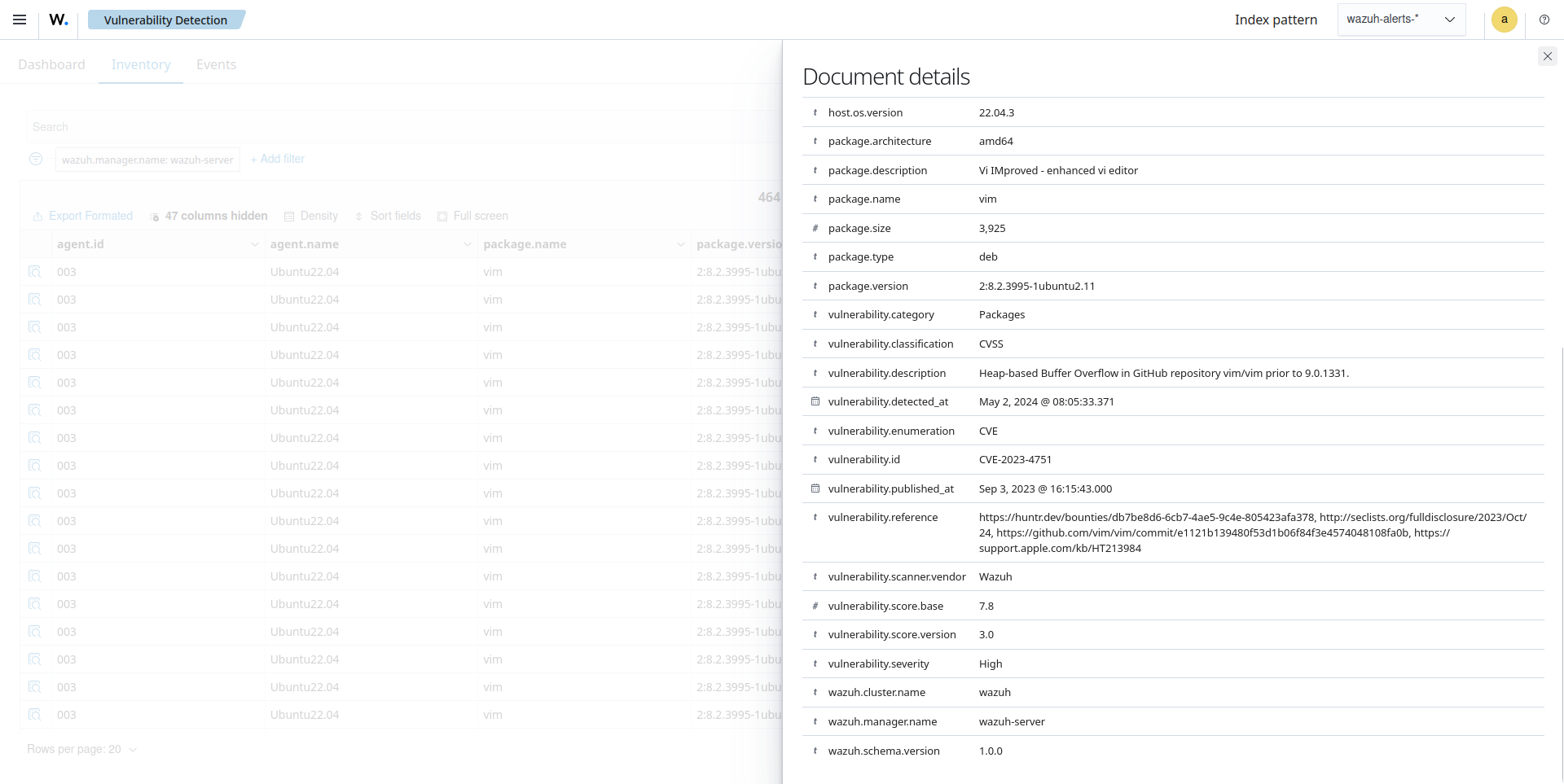
Once the scan finishes, you can see the results on the Wazuh dashboard. They include details of vulnerable packages, for example, vulnerabilities in the
firefoxapplication.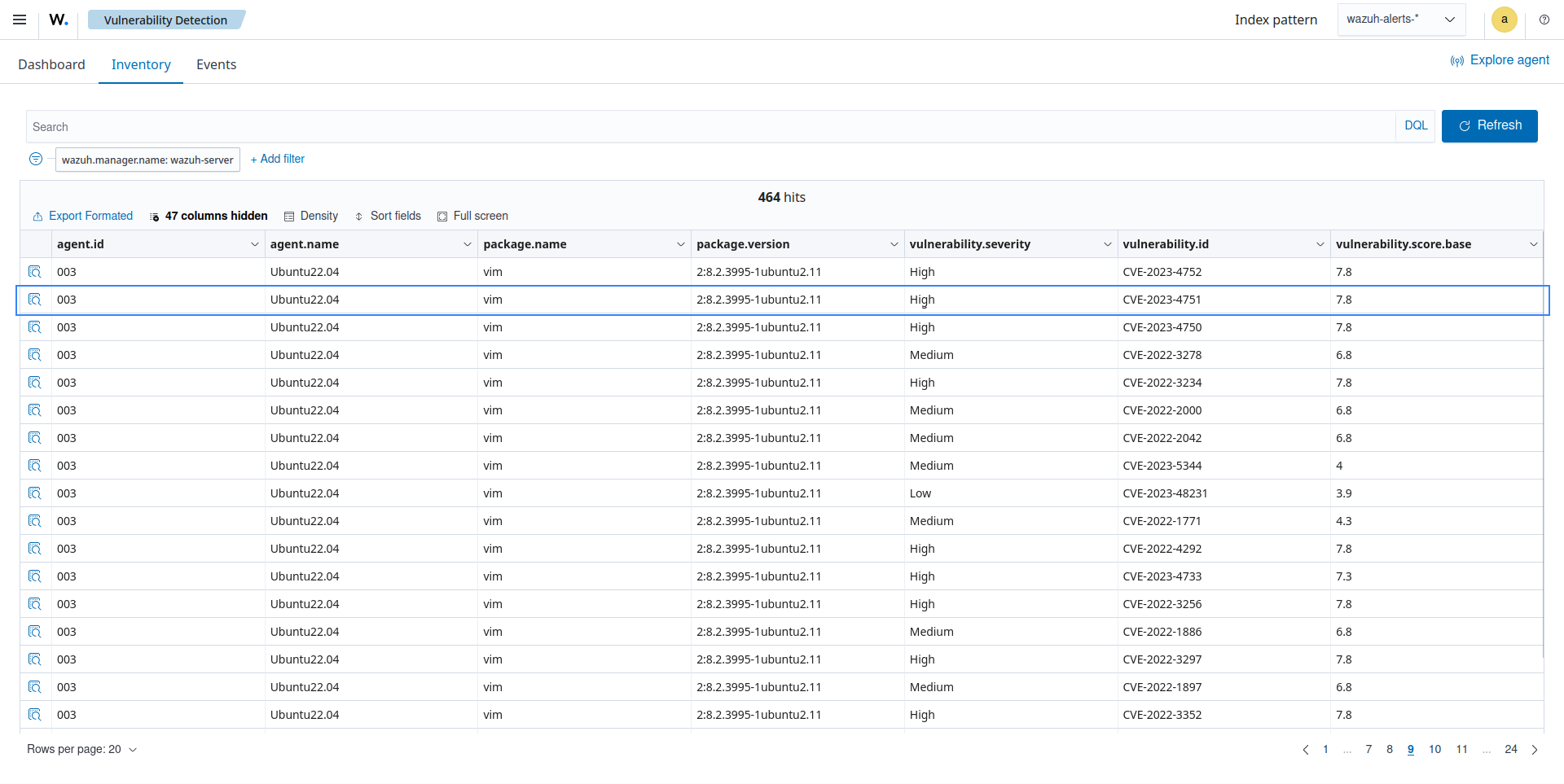
When you select any vulnerability, you see an overview of the detected issue and its status on the agent.
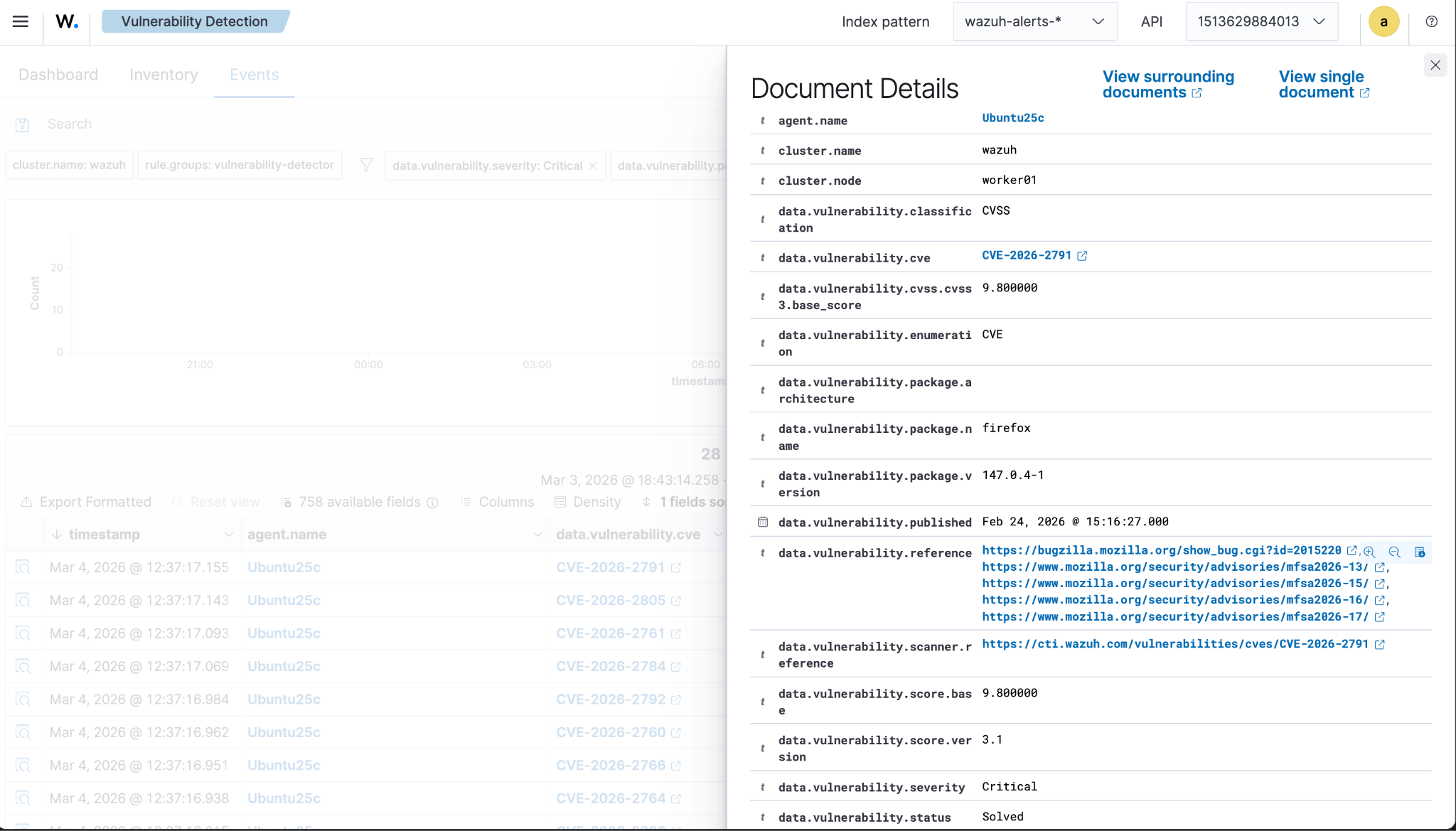
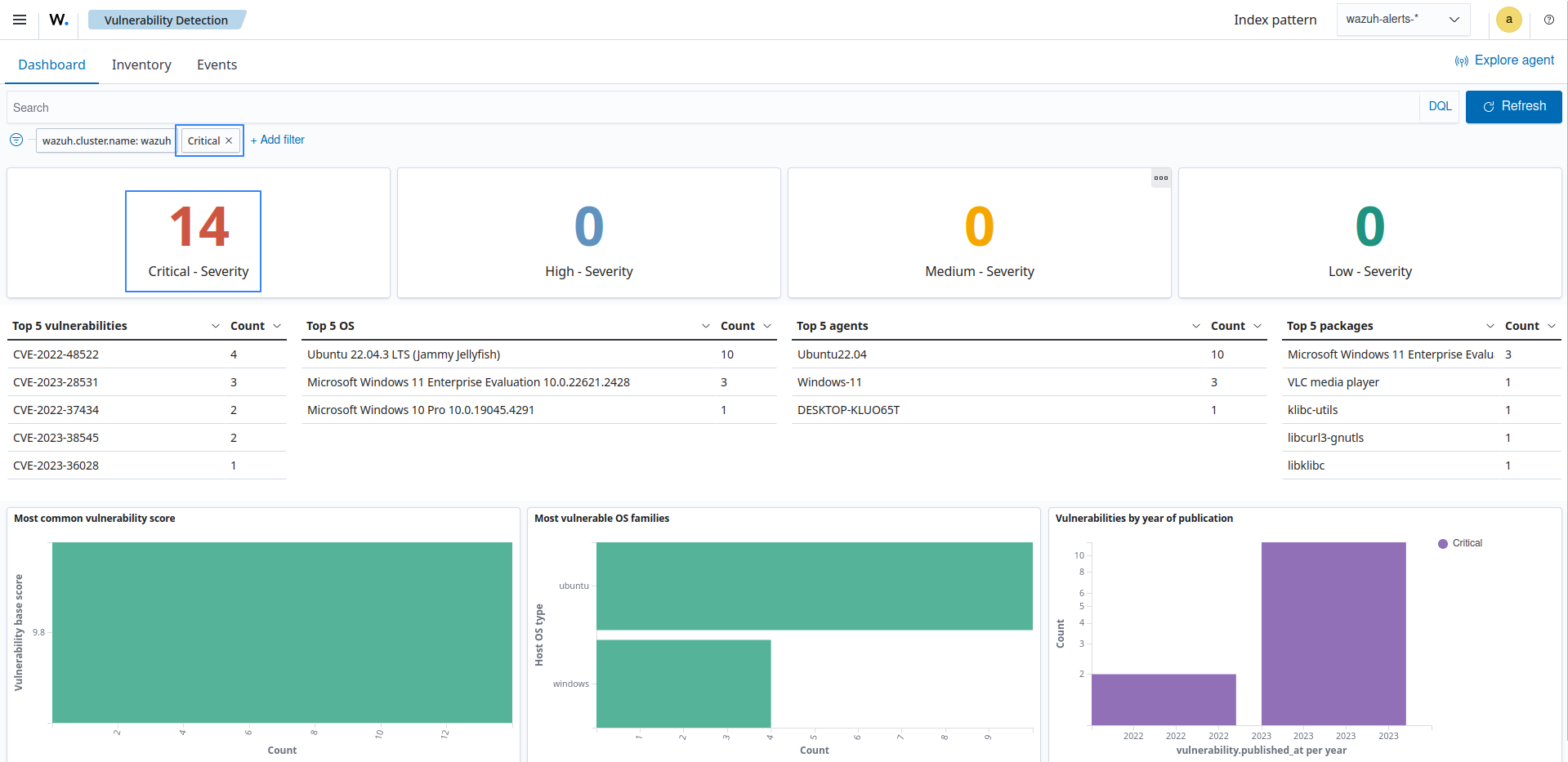
PCI DSS 11.3 requires that external and internal vulnerabilities be regularly identified, prioritized, and addressed. You can identify these vulnerabilities by performing vulnerability scans. The Wazuh vulnerability detector also supports prioritizing vulnerabilities by providing details on severity ratings and CVSS scores. On the vulnerability detector dashboard, it is possible to filter for vulnerabilities with a critical severity rating to prioritize remediation.