Network IDS integration
You can integrate Wazuh with Suricata, a network-based intrusion detection system (NIDS), to detect threats by monitoring network traffic. This solution can generate JSON logs of NIDS events and provide additional insight into your network's security with its network traffic inspection capabilities.
To see an example use case of a NIDS integration with Wazuh, go to the Catch suspicious network traffic section of the documentation.
Configuration
Configure your environment as follows to test the POC.
Install Suricata (tested with version 5.0.7) on the CentOS 8 monitored endpoint. This requires EPEL repository that depends on your operating system version.
yum install https://dl.fedoraproject.org/pub/epel/epel-release-latest-8.noarch.rpm yum -y install suricata-5.0.7
Download and extract Emerging rules.
cd /tmp/ curl -LO https://rules.emergingthreats.net/open/suricata-5.0.7/emerging.rules.tar.gz tar -xvzf emerging.rules.tar.gz && mv rules/*.rules /etc/suricata/rules/ chown suricata:suricata /etc/suricata/rules/*.rules chmod 777 /etc/suricata/rules/*.rules
Modify Suricata settings in the
/etc/suricata/suricata.yamlfile.EXTERNAL_NET: "any"default-rule-path: /etc/suricata/rules rule-files: - "*.rules"
Start Suricata.
systemctl enable suricata systemctl daemon-reload systemctl start suricata
Configure the Wazuh agent to read Suricata logs file. The following settings need to be added to the
/var/ossec/etc/ossec.conffile of the monitored CentOS 8 endpoint.<localfile> <log_format>syslog</log_format> <location>/var/log/suricata/eve.json</location> </localfile>
Restart the Wazuh agent to apply the changes.
systemctl restart wazuh-agent
Steps to generate the alerts
No action is required. Wazuh automatically parses data from /var/log/suricata/eve.json and generates related alerts.
Query the alerts
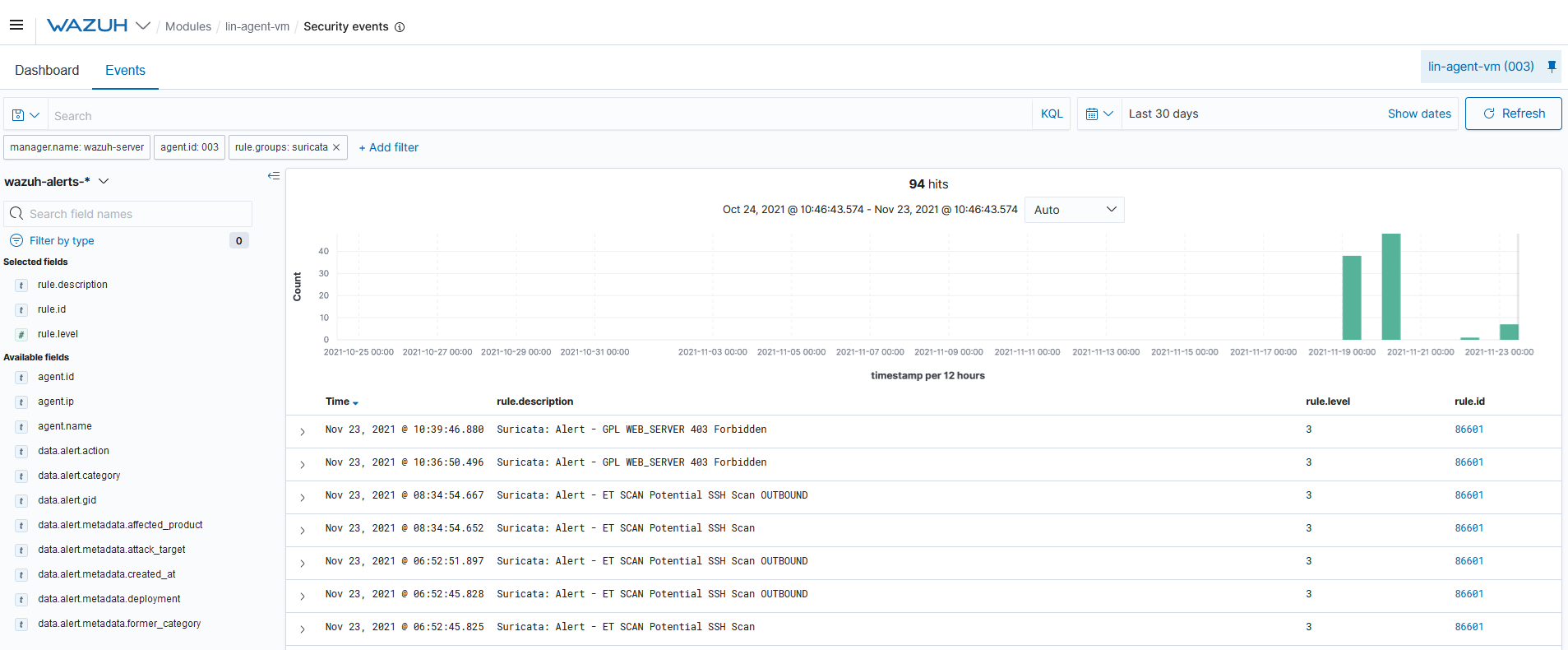
You can visualize the alert data in the Wazuh Kibana plugin. To do this, go to the Security events module and add the filters in the search bar to query the alerts.
rule.groups:suricata
Troubleshooting
Error concerning network interface in Suricata log file
/var/log/suricata/suricata.log.
To solve this issue, check the name of your network interface and configure it accordingly in the files /etc/sysconfig/suricata and /etc/suricata/suricata.yaml.