Custom Logs Buckets
Amazon Simple Queue Service (Amazon SQS) is a fully managed message queuing service. It offers secure, durable, and available hosted queues to decouple and scale software systems and components. It allows sending, storing, and receiving messages between software components at any volume, without losing messages or requiring other services to be available. These features make it an optimal component to associate with Amazon S3 buckets to consume any type of log.
Combining Amazon SQS with Amazon S3 buckets allows Wazuh to collect JSON, CSV, and plain text logs from any custom path. The origin of these logs don't even need to be AWS.
Note
To properly process CSV logs, they must include column headers.
To set up the Wazuh integration for Custom Logs Buckets, you need to do the following:
Create an AWS SQS Queue.
Configure an S3 bucket. For every object creation event, the bucket sends notifications to the queue.
AWS configuration
The following sections cover how to configure Custom Logs Buckets to integrate with Wazuh.
Amazon Simple Queue Service
Set up a Standard type SQS Queue with the default configurations. You can apply an Access Policy similar to the following example, where
<REGION>,<ACCOUNT_ID>,<SQS-NAME>, and<S3-BUCKET>are the region, account ID, the SQS Queue name, and the name you are going to provide to the S3 bucket.{ "Version": "2012-10-17", "Id": "example-ID", "Statement": [ { "Sid": "example-access-policy", "Effect": "Allow", "Principal": { "Service": "s3.amazonaws.com" }, "Action": "SQS:SendMessage", "Resource": "arn:aws:sqs:<REGION>:<ACCOUNT_ID>:<SQS-NAME>", "Condition": { "StringEquals": { "aws:SourceAccount": "<ACCOUNT_ID>" }, "ArnLike": { "aws:SourceArn": "arn:aws:s3:*:*:<S3-BUCKET>" } } } ] }
You can make your access policy to accept S3 notifications from different account IDs and to apply different conditions. More information in Managing access in Amazon SQS.
Amazon S3 and Event Notifications
To configure an S3 bucket that reports creation events, do the following.
Configure an S3 bucket as defined in the configuring an S3 bucket section. Provide the name you decided in the previous section.
Once created, go to Event notifications inside the Properties tab. Select Create event notification.
In Event Types, select All object create events. This generates notifications for any type of event that results in the creation of an object in the bucket.
In the Destination section, select the following options:
SQS queue
Choose from your SQS queues
Choose the queue you created previously.
Configuration parameters
Configure the following fields to set the queue and authentication configuration. For more information, check the subscribers reference.
Queue
<sqs_name>: The name of the queue.<service_endpoint>– Optional: The AWS S3 endpoint URL for data downloading from the bucket. Check Using VPC and FIPS endpoints for more information about VPC and FIPS endpoints.
Authentication
The available authentication methods are the following:
These authentication methods require using the /root/.aws/credentials file to provide credentials. You can find more information in configuring AWS credentials.
The available authentication configuration parameters are the following:
<aws_profile>: A valid profile name from a Shared Credential File or AWS Config File with permission to read logs from the bucket.<iam_role_arn>: Amazon Resource Name (ARN) for the corresponding IAM role to assume.<iam_role_duration>– Optional: The session duration in seconds.<sts_endpoint>– Optional: The URL of the VPC endpoint of the AWS Security Token Service.
Configure Wazuh to process logs from Custom Logs Buckets
Warning
Every message sent to the queue is read and deleted. Make sure you only use the queue for bucket notifications.
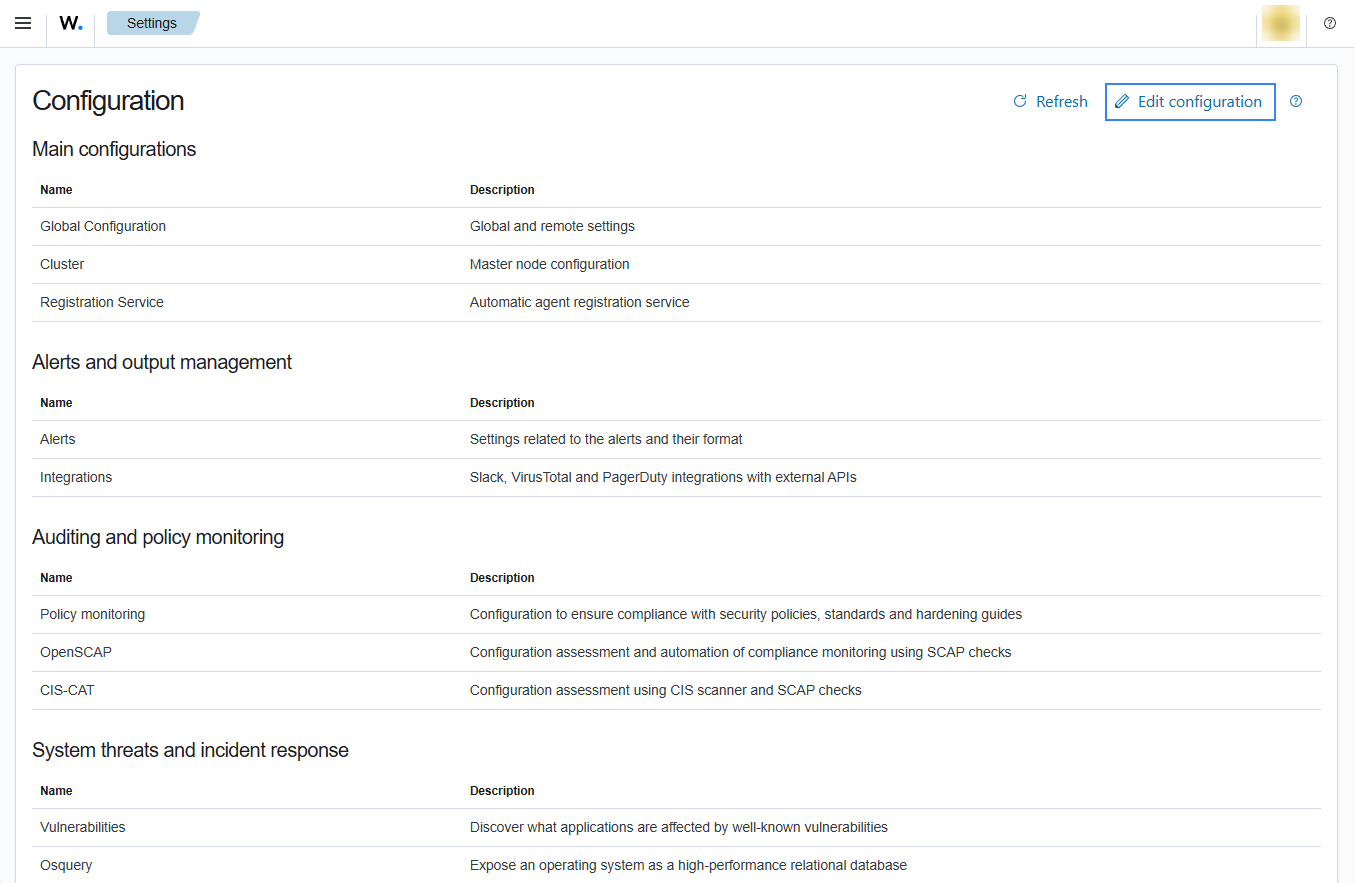
Access the Wazuh configuration in Server management > Settings using the Wazuh dashboard or by manually editing the
/var/ossec/etc/ossec.conffile in the Wazuh server or agent.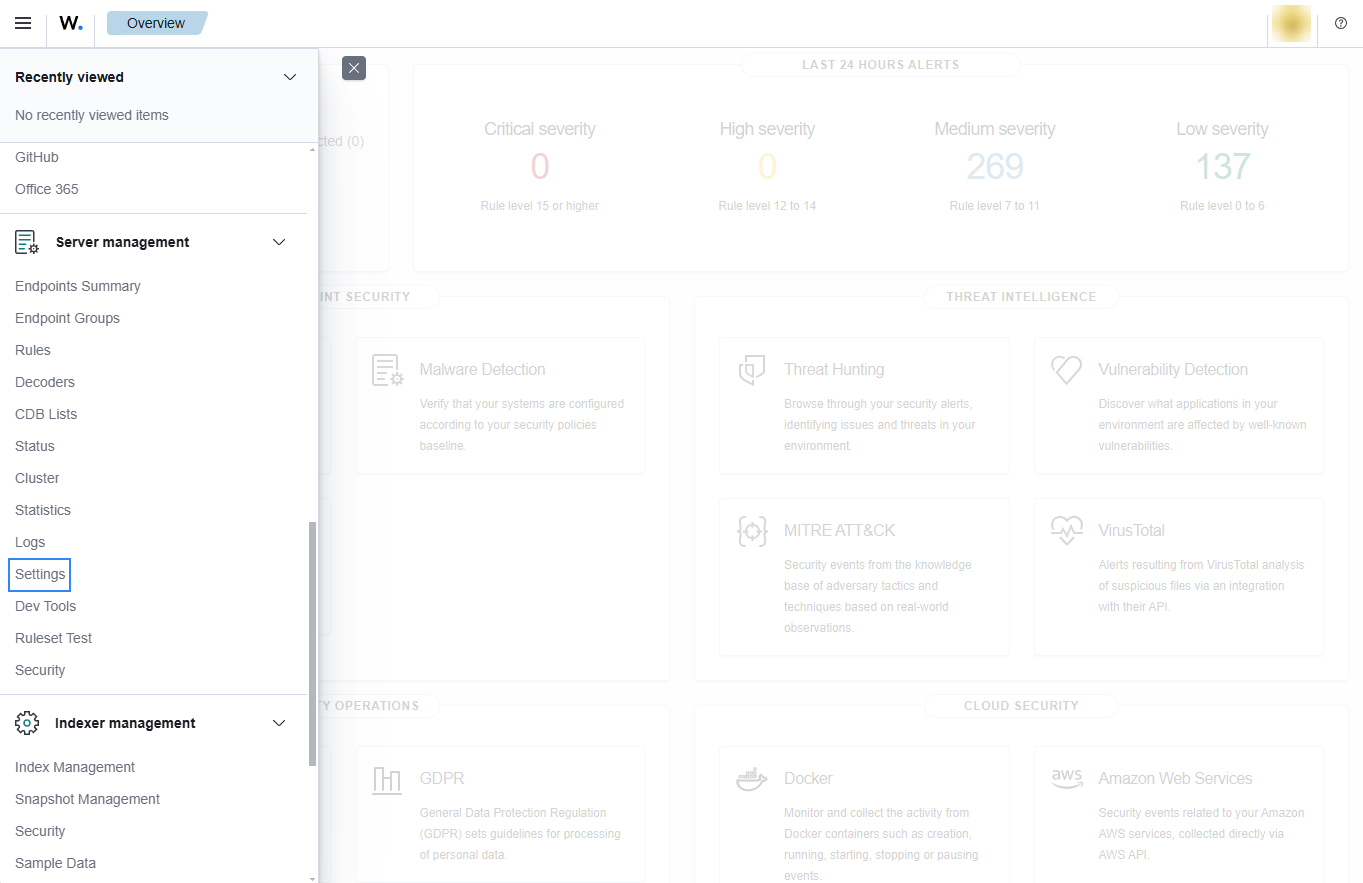
Add the SQS name and your configuration parameters for the buckets service. Set this inside
<subscriber type="buckets">. For example:<wodle name="aws-s3"> <disabled>no</disabled> <interval>1h</interval> <run_on_start>yes</run_on_start> <subscriber type="buckets"> <sqs_name>sqs-queue</sqs_name> <aws_profile>default</aws_profile> </subscriber> </wodle>
Check the Wazuh module for AWS reference manual to learn more about the available settings.
Note
The amount of notifications present in the queue affects the execution time of the Wazuh module for AWS. If the <interval> value for the waiting time between executions is too short, the interval overtaken warning is logged into the /var/ossec/logs/ossec.log file.
Save the changes and restart Wazuh to apply the changes. The service can be manually restarted using the following command outside the Wazuh dashboard:
Wazuh manager:
# systemctl restart wazuh-manager
Wazuh agent:
# systemctl restart wazuh-agent